Key Takeaways
- The Top 10 VPNs in the world in 2026 deliver near-native speeds, advanced encryption, and strong privacy protections for secure browsing, streaming, and remote work.
- Leading VPN providers like NordVPN, Surfshark, and Proton VPN combine post-quantum cryptography, AI-driven security, and independently audited no-logs policies.
- Choosing the best VPN in 2026 depends on your needs—whether it is privacy, streaming access, device compatibility, or enterprise-level cybersecurity protection.
The digital landscape in 2026 is defined by unprecedented connectivity, data-driven services, and an internet ecosystem that touches nearly every aspect of daily life. From remote work and cloud computing to global streaming platforms and online financial transactions, modern users rely heavily on secure internet access. At the same time, concerns surrounding privacy, cybersecurity threats, data surveillance, and online censorship have grown dramatically. In this environment, Virtual Private Networks have become one of the most essential technologies for protecting digital activity and maintaining online freedom.

A VPN creates an encrypted tunnel between a user’s device and the internet, masking the user’s IP address while protecting their data from interception. This technology allows individuals and organizations to browse securely, protect sensitive information, and access global content without exposing their identity or location. Over the past decade, VPN adoption has moved far beyond niche cybersecurity communities and entered the mainstream, becoming a standard tool for secure internet use across households, businesses, and governments.
The year 2026 represents a particularly significant milestone for the VPN industry. Rapid advancements in cybersecurity technologies, increasing government regulation, artificial intelligence–driven threat detection, and the looming influence of quantum computing have transformed the way VPN services are developed and evaluated. Modern VPN providers must deliver not only high-speed encrypted connections but also advanced security architectures capable of adapting to emerging digital threats.
Why VPNs Are More Important Than Ever in 2026
The growing demand for VPN services is driven by several key developments in the global digital ecosystem. Cybercrime has evolved into a highly organized industry, with sophisticated attacks targeting both individuals and enterprises. Data breaches, phishing campaigns, ransomware operations, and identity theft incidents have become increasingly common, making cybersecurity tools essential for everyday internet users.
At the same time, online privacy has become a central concern for millions of people worldwide. Governments, advertisers, and technology companies collect vast amounts of user data through tracking technologies, behavioral analytics, and algorithmic monitoring systems. Without proper protection, personal information such as browsing history, location data, and communication patterns can be exposed or exploited.
VPN technology provides a powerful solution to many of these challenges by encrypting internet traffic and routing it through secure servers located around the world. This process helps prevent third parties from monitoring online activity while allowing users to maintain greater control over their digital identity.
Key Reasons People Use VPNs in 2026
Purpose of VPN Use | Description
Online Privacy Protection | Prevents tracking and protects personal data from surveillance
Secure Public Wi-Fi Access | Encrypts connections on unsecured networks such as cafes or airports
Streaming Content Access | Enables users to access region-restricted streaming platforms
Remote Work Security | Allows employees to securely connect to corporate networks
Bypassing Censorship | Helps users access unrestricted information in regions with internet controls
These practical benefits explain why VPN adoption has increased dramatically across both consumer and enterprise markets in recent years.
The Evolution of the VPN Industry
The VPN industry in 2026 is far more sophisticated than it was just a decade ago. Early VPN services focused primarily on basic encryption and IP masking. While these features remain fundamental, modern VPN platforms now incorporate a wide range of advanced security technologies designed to protect users against increasingly complex threats.

Many of the leading VPN providers now integrate artificial intelligence to monitor network traffic, detect anomalies, and optimize server routing for improved performance. AI-driven systems can dynamically adjust infrastructure resources, predict congestion, and defend against automated cyberattacks.
Another major transformation involves the adoption of post-quantum cryptographic algorithms. As research into quantum computing continues to accelerate, cybersecurity experts are preparing for the possibility that traditional encryption methods could eventually become vulnerable to quantum-based decryption techniques. To address this risk, several top VPN providers have begun implementing quantum-resistant encryption protocols designed to protect data far into the future.
These technological advancements demonstrate that the VPN industry is no longer focused solely on secure connectivity. Instead, it has evolved into a complex cybersecurity ecosystem that combines encryption, network optimization, privacy protection, and identity security into a single service platform.
Key Technologies Shaping VPN Services in 2026
Technology | Role in Modern VPN Infrastructure
Post-Quantum Cryptography | Protects encryption systems against future quantum computing threats
Artificial Intelligence Security | Monitors network traffic and detects cyber threats automatically
WireGuard-based Protocols | Provides faster, more efficient encrypted connections
Stealth and Obfuscation Protocols | Allows VPN traffic to bypass deep packet inspection systems
Zero-Trust Security Integration | Enhances enterprise network access control and authentication
These technologies represent the next generation of secure networking tools and play a major role in determining which VPN providers lead the market.
What Defines the Best VPNs in 2026
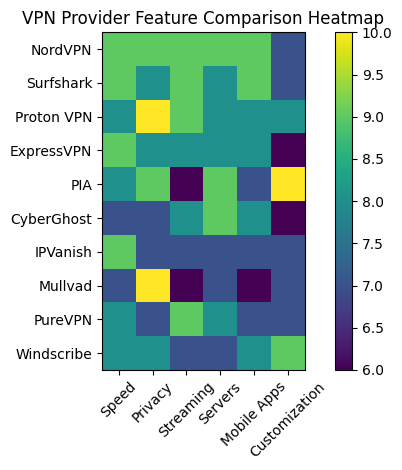
With hundreds of VPN services available globally, selecting the best VPN providers requires evaluating multiple performance and security factors. Speed, encryption standards, server coverage, transparency, mobile compatibility, and streaming performance all contribute to the overall effectiveness of a VPN service.
The top VPN providers in 2026 are distinguished by their ability to deliver consistently fast connections while maintaining strong privacy protections and reliable global infrastructure. Many leading providers operate thousands of servers across dozens of countries, ensuring users can maintain stable connections regardless of location.
Another important factor is transparency. Reputable VPN services now undergo independent security audits conducted by third-party cybersecurity firms to verify their no-logs policies and infrastructure security. These audits help build trust by demonstrating that providers do not collect or store user activity data.
Evaluation Criteria for the Best VPN Services
Evaluation Factor | Importance for Users
Connection Speed | Determines streaming, gaming, and browsing performance
Encryption Strength | Protects sensitive data from interception
No-Logs Policy | Ensures user activity is not stored or tracked
Server Network Size | Improves connection stability and global accessibility
Mobile App Performance | Essential as most VPN usage now occurs on smartphones
Independent Security Audits | Provides external verification of privacy claims
These factors are used by industry analysts and cybersecurity experts when comparing VPN services worldwide.
Overview of the Top VPN Providers in 2026
The top VPN providers in the world in 2026 include a diverse range of services, each offering unique advantages for different types of users. Some prioritize privacy and anonymity, while others focus on speed, streaming compatibility, or enterprise-grade network security.
Among the most recognized providers are NordVPN, Surfshark, Proton VPN, ExpressVPN, Private Internet Access, CyberGhost, IPVanish, Mullvad VPN, PureVPN, and Windscribe. These services consistently rank among the best in the industry due to their advanced features, global server infrastructure, and strong reputations for privacy protection.
While each VPN service has its own strengths, they all share several important characteristics: robust encryption standards, reliable network performance, transparent privacy policies, and strong compatibility with modern devices and operating systems.
The Importance of Choosing the Right VPN
Selecting the right VPN provider can significantly impact both online security and user experience. A high-quality VPN ensures that internet traffic remains private while maintaining fast and stable connections for everyday activities such as browsing, streaming, and remote work.
However, not all VPN services provide the same level of protection or reliability. Some providers may lack strong encryption standards, operate limited server networks, or collect user data despite claiming to offer privacy protection. For this reason, thorough research and comparison are essential before choosing a VPN service.
This comprehensive guide explores the top 10 VPNs in the world in 2026, analyzing their performance, security features, infrastructure capabilities, and overall value. By examining each provider in detail, readers can better understand which VPN services offer the most effective solutions for privacy, security, and unrestricted internet access in today’s increasingly complex digital environment.
As cybersecurity threats continue to evolve and online privacy becomes more difficult to maintain, VPN technology will remain a critical component of safe and secure internet usage. The providers that combine innovation, transparency, and strong technical performance will define the future of digital privacy in the years ahead.
Top 10 VPNs in the World in 2026
- NordVPN
- Surfshark
- Proton VPN
- ExpressVPN
- Private Internet Access (PIA)
- CyberGhost
- IPVanish
- Mullvad VPN
- PureVPN
- Windscribe
1. NordVPN
The virtual private network industry has evolved significantly by 2026, transforming from a niche privacy tool into a mainstream cybersecurity solution used by individuals, businesses, and remote professionals worldwide. Modern VPN services now extend far beyond simple IP masking. They function as integrated security platforms that combine encrypted networking, threat detection, identity protection, secure cloud storage, and privacy auditing.
As global internet surveillance, data harvesting, and cybercrime continue to increase, VPN adoption has accelerated across both developed and emerging markets. Consumers rely on VPNs to secure remote work connections, protect personal information on public Wi-Fi networks, bypass regional content restrictions, and maintain anonymity while browsing online. Enterprises and digital professionals increasingly deploy VPNs as part of broader cybersecurity infrastructure.
By 2026, the most competitive VPN providers operate vast global server networks, employ next-generation encryption protocols, and undergo independent security audits to validate their privacy claims. The leading services are evaluated based on several factors including server infrastructure, connection speeds, privacy jurisdiction, encryption standards, streaming capability, and the breadth of integrated cybersecurity tools.
Among the top VPN services globally, NordVPN continues to hold a dominant position due to its extensive infrastructure, high-performance network protocols, and expanding security ecosystem.
Overview of NordVPN as a Leading VPN Service
NordVPN remains one of the most widely recognized and technically advanced VPN providers in 2026. The service has built a reputation as a comprehensive digital security platform rather than merely a privacy tool. Its ecosystem now integrates VPN connectivity with password management, malware protection, encrypted cloud storage, and identity monitoring services.
Headquartered in Panama, NordVPN benefits from a favorable privacy jurisdiction. Panama is not part of the 5 Eyes, 9 Eyes, or 14 Eyes intelligence-sharing alliances, which means the company operates outside many international surveillance frameworks. This jurisdictional advantage reinforces its commitment to maintaining strict user privacy and enforcing a verified no-logs policy.
The provider’s network infrastructure has expanded dramatically, now consisting of more than 9,000 servers distributed across approximately 130 countries. Many of these servers have been upgraded with high-capacity 10 Gbps and 100 Gbps network cards, significantly reducing network congestion while enabling high-bandwidth activities such as ultra-high-definition streaming, large file transfers, and online gaming.
NordVPN Infrastructure and Network Distribution
The size and technological capability of a VPN’s server network plays a crucial role in maintaining connection reliability and minimizing latency. NordVPN’s infrastructure in 2026 reflects a highly distributed and performance-focused architecture.
Global Infrastructure Overview
| Infrastructure Category | Specification Description |
|---|---|
| Total Servers | Over 9,000 servers worldwide |
| Countries Covered | Approximately 130 countries |
| Network Card Capacity | 10 Gbps and 100 Gbps upgraded servers |
| Server Types | Standard VPN, Double VPN, Onion over VPN, P2P optimized |
| Infrastructure Model | Combination of owned and colocated hardware |
| Privacy Jurisdiction | Panama |
| Logging Policy | Verified independent no-logs policy |
This large-scale deployment allows NordVPN to maintain stable connection performance across North America, Europe, Asia-Pacific, the Middle East, and emerging digital markets in Africa and Latin America.
Performance and Speed Benchmarks in 2026
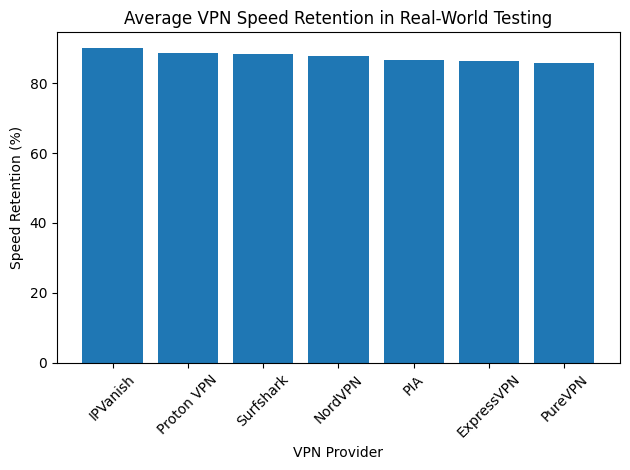
Speed performance is a critical factor in VPN adoption, particularly for users engaging in high-bandwidth applications such as 4K streaming, cloud gaming, and large file synchronization. NordVPN’s proprietary NordLynx protocol, built around the WireGuard architecture, continues to be a key factor behind its high-performance network capabilities.
Independent speed tests conducted in early 2026 reveal that NordVPN maintains extremely low speed loss and minimal latency compared with other major VPN providers.
Performance Benchmark Matrix
| Test Metric | Result Observed |
|---|---|
| Average Download Retention | 87.8% |
| Test Line Speed | 100 Mbps |
| Recorded Download Speed | 98.5 Mbps |
| Speed Loss | 1.5% |
| Average Latency | 1 millisecond |
| Streaming Capability | 4K / Ultra HD |
| Gaming Suitability | High |
These results position NordVPN among the fastest VPN services globally, making it suitable for everyday internet use without noticeable performance degradation.
NordVPN Security Ecosystem
In addition to VPN connectivity, NordVPN has expanded its cybersecurity ecosystem with advanced security modules designed to protect users against modern digital threats.
One of its most significant developments is the evolution of its Threat Protection Pro system. Originally introduced as an ad and tracker blocker, the feature has matured into a multi-layered security tool capable of scanning downloads, blocking malicious websites, filtering trackers, and preventing phishing attempts.
A notable characteristic of Threat Protection Pro is that it continues to function even when the VPN connection itself is disabled. This design allows the feature to operate as a lightweight antivirus-like protection layer within the broader NordVPN software suite.
Security Feature Matrix
| Security Feature | Functional Description |
|---|---|
| AES-256 Encryption | Military-grade encryption for data transmission |
| NordLynx Protocol | High-speed WireGuard-based connection protocol |
| Threat Protection Pro | Malware blocking, phishing protection, tracker filtering |
| Kill Switch | Automatic disconnection if VPN drops |
| Double VPN | Multi-hop encryption through two VPN servers |
| Onion over VPN | Integration with the Tor anonymity network |
| Dark Web Monitoring | Alerts for compromised credentials |
| RAM-only Servers | Servers that erase data on reboot |
These features collectively position NordVPN as a hybrid between a privacy network and a full cybersecurity toolkit.
NordVPN Pricing Structure and Subscription Tiers
NordVPN employs a tiered pricing model that bundles additional security tools into progressively more comprehensive subscription packages. Long-term subscription plans often provide the most significant value for consumers.
Subscription Plan Comparison
| Plan Tier | Monthly Cost (2-Year Plan) | Renewal Cost Trend | Maximum Devices | Included Features |
|---|---|---|---|---|
| Basic | $3.39 | Higher on renewal | 10 devices | Core VPN functionality |
| Plus | $4.39 | Higher on renewal | 10 devices | VPN + password manager + breach scanner |
| Complete | $5.39 | Higher on renewal | 10 devices | VPN + NordPass + encrypted 1 TB cloud storage |
| Prime | $7.39 | Higher on renewal | 10 devices | Full bundle + identity protection + cyber insurance |
The bundled approach reflects a growing trend in the cybersecurity industry where VPN providers expand into broader digital security ecosystems.
Strategic Marketing and Subscription Incentives
In recent years, NordVPN has also implemented aggressive promotional strategies to encourage longer subscription commitments. These strategies often include bundled software packages and promotional incentives such as digital gift cards.
Long-term subscribers frequently receive value-added extras such as:
| Incentive Type | Description |
|---|---|
| Gift Card Promotions | Limited-time Amazon gift card rewards |
| Multi-Tool Bundles | Integration with NordPass and NordLocker services |
| Extended Trial Guarantees | Risk-free refund periods for new subscribers |
| Family Device Coverage | Support for multiple simultaneous devices |
These promotional offers are designed to improve user retention while positioning NordVPN as an all-in-one digital protection platform.
Independent Privacy Audits and Trust Verification
Trust is a central issue in the VPN industry. To reinforce transparency, NordVPN regularly commissions independent audits of its infrastructure and privacy policies.
As of 2026, NordVPN has completed five independent no-logs audits conducted by reputable cybersecurity auditing firms. The most recent audit was performed by Deloitte in 2025, which confirmed that NordVPN does not log identifiable user activity.
Privacy Verification Summary
| Audit Element | Details |
|---|---|
| Number of Independent Audits | 5 completed audits |
| Latest Audit Year | 2025 |
| Auditing Organization | Deloitte |
| Audit Focus | Verification of no-logs policy |
| Server Architecture | RAM-only diskless infrastructure |
Regular third-party verification has become an industry standard among top VPN providers, helping build credibility with privacy-conscious users.
Position of NordVPN in the Global VPN Market
In the broader context of the Top 10 VPN services worldwide in 2026, NordVPN continues to lead due to its balance of speed, privacy jurisdiction, security features, and integrated cybersecurity tools. Its combination of high-performance infrastructure, independently verified privacy policies, and multi-layered security services places it among the most comprehensive VPN platforms currently available.
While the global VPN market includes several strong competitors offering specialized features or lower pricing, NordVPN remains widely regarded as the benchmark service for users seeking a well-rounded, high-performance VPN solution suitable for both everyday browsing and advanced digital security needs.
2. Surfshark
Within the competitive landscape of the Top VPN services in 2026, Surfshark has emerged as one of the most attractive options for users seeking high performance at a comparatively lower price point. While many premium VPN providers position themselves around advanced enterprise-grade security features, Surfshark differentiates itself through an aggressive value-oriented model combined with strong technical capabilities.
The provider has successfully positioned itself as a household-friendly VPN solution, particularly appealing to families, remote workers, and multi-device households. One of its defining advantages is the ability to support unlimited simultaneous device connections under a single subscription. This rare feature eliminates the need for multiple accounts and allows users to protect every device within a home or small office network.
Headquartered in the Netherlands, Surfshark operates within the European privacy regulatory environment. Despite the Netherlands being associated with certain intelligence-sharing alliances, Surfshark maintains strict internal privacy practices and supports its claims through regular independent audits.
Global Infrastructure and Server Distribution
As the demand for fast and geographically diverse VPN connections has increased, Surfshark has expanded its infrastructure considerably. By 2026, the company operates a network of more than 4,500 servers across approximately 100 countries. These servers are entirely RAM-only, meaning they store no permanent data and automatically wipe information whenever they reboot.
RAM-only infrastructure has become a critical privacy safeguard within the VPN industry because it prevents any long-term storage of user activity data.
Surfshark Global Infrastructure Overview
| Infrastructure Category | Specification Description |
|---|---|
| Total Servers | 4,500+ RAM-only servers |
| Countries Covered | 100 countries |
| Server Architecture | Diskless RAM-only infrastructure |
| Device Connection Limit | Unlimited devices per subscription |
| VPN Protocol Support | WireGuard, OpenVPN, IKEv2 |
| Encryption Standards | AES-256 and ChaCha20 |
| Company Headquarters | Netherlands |
| Privacy Audits | Independent third-party audits |
The wide geographic coverage allows users to access region-specific content libraries, maintain low latency connections, and reduce network congestion during peak usage hours.
Performance and Speed Benchmarks in 2026
Despite being marketed as a budget-friendly VPN service, Surfshark consistently ranks among the fastest VPN providers globally. Recent performance tests conducted in 2026 show that the service delivers exceptional download retention and extremely low latency.
Interestingly, its download retention score slightly surpasses NordVPN in some benchmarking scenarios, highlighting the efficiency of its server optimization and network routing strategies.
Speed Performance Benchmark Matrix
| Performance Metric | Result Observed |
|---|---|
| Average Download Retention | 88.3% |
| Average Latency | 2 milliseconds |
| Test Connection Speed | 100 Mbps line |
| Connection Stability | Very High |
| Streaming Compatibility | Ultra HD / 4K |
| Gaming Suitability | High |
These results demonstrate that Surfshark is capable of supporting bandwidth-heavy activities including high-definition video streaming, online multiplayer gaming, and large file downloads.
Core Technical Specifications
Surfshark integrates modern encryption standards and optimized connection protocols to deliver both security and performance. Its protocol architecture allows users to choose between different tunneling technologies depending on their specific requirements.
Encryption and Connection Technology
| Technology Category | Implementation Details |
|---|---|
| Primary Encryption | AES-256-GCM |
| Alternative Encryption | ChaCha20 |
| VPN Protocols Supported | WireGuard, OpenVPN, IKEv2 |
| Data Authentication | SHA-512 hash authentication |
| Perfect Forward Secrecy | Enabled across supported protocols |
| Network Kill Switch | Automatic traffic shutdown if VPN disconnects |
These technologies collectively ensure that data transmissions remain encrypted, authenticated, and protected from interception.
Nexus Technology and Advanced Networking Innovation
One of Surfshark’s most distinctive innovations is its proprietary networking architecture known as Nexus. Unlike traditional VPN routing systems that assign a single static VPN server during a session, Nexus introduces a software-defined networking layer that distributes user traffic across multiple servers dynamically.
This design enables several advanced capabilities:
• Seamless IP rotation without disconnecting the VPN session
• Customizable multi-hop server routes
• Improved load balancing across the network
• Reduced detection by anti-VPN filtering systems
Nexus Architecture Capabilities
| Nexus Feature | Functional Benefit |
|---|---|
| Dynamic IP Rotation | Regularly changes the user’s IP address |
| Multi-Hop Routing | Routes traffic through multiple VPN servers |
| Server Load Balancing | Optimizes connection stability and speed |
| Session Persistence | Maintains connection without manual reconnection |
| Network-Level Privacy Layer | Adds additional anonymity to VPN traffic |
This technology significantly improves both anonymity and reliability, particularly for users who require continuous connections for remote work or secure browsing.
Security Suite and Privacy Protection Tools
Surfshark complements its VPN functionality with a collection of privacy-focused security tools designed to mitigate common online threats such as trackers, spam, phishing attempts, and malicious websites.
Key components of Surfshark’s security suite include CleanWeb and Alternative ID.
Security Feature Ecosystem
| Security Tool | Functional Description |
|---|---|
| CleanWeb | Blocks advertisements, trackers, malware domains, and phishing sites |
| Alternative ID | Generates disposable online identities and email addresses |
| Kill Switch | Automatically disconnects traffic if VPN connection drops |
| Multi-Hop VPN | Routes traffic through multiple VPN servers for added privacy |
| Camouflage Mode | Masks VPN usage to bypass restrictive networks |
| NoBorders Mode | Enables VPN access in restrictive regions |
The Alternative ID feature has become particularly popular among privacy-conscious users because it helps reduce spam exposure when registering for online services or newsletters.
Pricing Strategy and Subscription Value
Surfshark’s pricing model is one of the most competitive in the industry, allowing the company to attract users who want strong VPN capabilities without committing to higher-priced premium services.
Surfshark Pricing Overview
| Pricing Category | Details |
|---|---|
| Starting Price | $1.99 per month (2-year subscription) |
| Device Limit | Unlimited devices |
| Free Trial | Available on select platforms |
| Refund Guarantee | 30-day money-back guarantee |
| Long-Term Discount Plans | Substantial savings on multi-year plans |
Because the subscription allows unlimited device connections, households with multiple smartphones, laptops, smart TVs, and gaming consoles often find Surfshark to be one of the most cost-effective VPN services available.
Independent Audits and Transparency
Trust is a critical factor when selecting a VPN provider. Surfshark has attempted to strengthen its credibility by undergoing independent audits that verify its infrastructure and privacy claims.
In 2025, the company completed a no-logs policy verification conducted by Deloitte, one of the leading global auditing firms. The audit confirmed that Surfshark does not retain user activity logs that could compromise customer privacy.
Privacy Audit Verification
| Audit Attribute | Details |
|---|---|
| Independent Auditor | Deloitte |
| Audit Completion Year | 2025 |
| Policy Verified | Strict no-logs policy |
| Infrastructure Examined | VPN server environment and logging |
| Compliance Outcome | Verified adherence to privacy claims |
Regular third-party security audits have become increasingly important in the VPN industry, as they provide external validation that a provider’s privacy policies match its technical implementation.
Surfshark’s Position Among the Top VPN Services in 2026
In the broader comparison of the Top 10 VPN services globally in 2026, Surfshark occupies a unique position. It combines strong technical performance with highly competitive pricing while offering features that are rarely available elsewhere in the industry, particularly unlimited device connections and advanced network routing technologies like Nexus.
For households, small teams, and privacy-conscious users seeking maximum coverage across multiple devices, Surfshark represents one of the most balanced VPN solutions available in terms of cost, performance, and modern cybersecurity features.
3. Proton VPN
Among the leading virtual private network providers in 2026, Proton VPN has established itself as one of the most trusted platforms for users who prioritize transparency, privacy protection, and advanced security architecture. Developed by the same organization behind Proton Mail, Proton VPN was created with a strong emphasis on privacy-first infrastructure, open-source transparency, and jurisdictional protection.
Unlike many commercial VPN services that primarily focus on entertainment streaming and casual browsing, Proton VPN is widely recognized for its appeal among privacy advocates, cybersecurity professionals, and technically advanced users. The service combines strict privacy policies, open-source development, and a high-performance global server infrastructure designed to protect users from surveillance, censorship, and cyber threats.
Based in Switzerland, Proton VPN benefits from one of the most privacy-friendly legal environments in the world. Switzerland’s strict data protection laws and strong legal safeguards against external surveillance requests provide an additional layer of protection for user data. This jurisdictional advantage is a key reason Proton VPN is often recommended for journalists, activists, and individuals seeking strong anonymity online.
Global Infrastructure and Network Expansion
By 2026, Proton VPN has significantly expanded its server infrastructure, making it one of the largest networks among premium VPN providers. The service now operates more than 18,100 servers distributed across over 120 countries. This expansion allows Proton VPN to maintain stable connection speeds, reduce server congestion, and provide reliable geographic coverage for users worldwide.
Large server networks play an important role in maintaining connection quality because they distribute user traffic efficiently while minimizing network bottlenecks.
Proton VPN Infrastructure Overview
| Infrastructure Category | Specification Description |
|---|---|
| Total Servers | Over 18,100 servers |
| Geographic Coverage | 120+ countries |
| Data Center Security | Hardened and physically secured facilities |
| Server Types | Standard, Secure Core, P2P optimized |
| VPN Protocols Supported | WireGuard, OpenVPN, IKEv2, Stealth |
| Company Headquarters | Switzerland |
| Privacy Jurisdiction | Swiss data protection laws |
The extensive global network ensures that Proton VPN users can connect to geographically diverse servers while maintaining stable performance for browsing, streaming, gaming, and file transfers.
Performance and Speed Capabilities
Although Proton VPN is traditionally known for privacy features rather than raw speed, its technological innovations have significantly improved network performance. Independent performance tests conducted in 2026 show that Proton VPN achieves an impressive download retention score of approximately 88.6 percent.
A major factor behind this improvement is Proton VPN’s proprietary VPN Accelerator technology. This system optimizes TCP and UDP traffic flows by dynamically adjusting routing paths and reducing latency issues across long-distance connections.
VPN Accelerator is particularly effective in regions where network latency is naturally high, such as cross-continental connections or networks experiencing bandwidth congestion.
Speed Performance Benchmark Matrix
| Performance Metric | Observed Result |
|---|---|
| Average Download Retention | 88.6% |
| Latency Optimization Technology | VPN Accelerator |
| Streaming Capability | Ultra HD / 4K |
| Long-Distance Connection Speed | Significantly optimized |
| Gaming Stability | High |
These performance improvements allow Proton VPN to compete directly with the fastest commercial VPN providers while maintaining its privacy-focused architecture.
Secure Core Architecture and Multi-Layer Privacy
One of Proton VPN’s most distinctive features is its Secure Core architecture. Unlike traditional VPN services that route traffic through a single server, Secure Core introduces an additional security layer by routing traffic through multiple hardened servers located in privacy-friendly countries.
These Secure Core servers are located in physically secured data centers within Switzerland, Sweden, and Iceland. These facilities are designed to protect against both digital attacks and physical tampering.
Secure Core Architecture Workflow
| Routing Stage | Function |
|---|---|
| Entry Server | Receives encrypted user traffic |
| Secure Core Server | Routes traffic through hardened privacy jurisdiction |
| Exit Server | Connects to the public internet |
| Encryption Layer | End-to-end encrypted tunnel maintained |
This architecture protects users against traffic correlation attacks and compromised exit nodes, providing an additional level of anonymity not commonly found in conventional VPN services.
Open-Source Transparency and Security Philosophy
Proton VPN stands out in the industry due to its strong commitment to open-source transparency. All major Proton VPN applications are fully open-source, allowing security researchers, independent developers, and privacy advocates to inspect the codebase for potential vulnerabilities.
Open-source development has become an important trust mechanism in the cybersecurity industry because it allows public verification of software behavior rather than requiring blind trust in proprietary systems.
Transparency and Security Practices
| Transparency Feature | Implementation Details |
|---|---|
| Open-Source Applications | All major client apps publicly available |
| Independent Security Audits | Regular third-party code reviews |
| No-Logs Policy | Court-tested privacy policy |
| Transparency Reports | Public disclosure of legal requests |
| Community Security Reviews | Continuous inspection by cybersecurity researchers |
These transparency practices strengthen Proton VPN’s reputation as one of the most trustworthy VPN services in operation.
Advanced Networking Features for Power Users
Proton VPN provides several advanced networking capabilities designed specifically for technically inclined users and performance-sensitive applications. One of the most notable features is integrated port forwarding.
Port forwarding enables users to open specific network ports through the VPN tunnel, allowing improved connectivity for peer-to-peer file transfers, gaming servers, and certain remote access applications.
Advanced Networking Feature Matrix
| Feature | Functional Benefit |
|---|---|
| Port Forwarding | Improves torrenting speeds and gaming connectivity |
| Split Tunneling | Allows selected apps to bypass VPN routing |
| Secure Core Routing | Multi-hop privacy routing architecture |
| VPN Accelerator | Improved performance across long-distance networks |
| DNS Leak Protection | Prevents exposure of browsing activity |
Because of these capabilities, Proton VPN is widely considered one of the most powerful VPN platforms for advanced users.
Stealth Protocol and Anti-Censorship Technology
Proton VPN has also developed specialized technologies for bypassing internet censorship. Its Stealth protocol is designed to disguise VPN traffic so that it appears as normal encrypted web traffic.
This feature is particularly valuable in countries where VPN usage is restricted or heavily monitored using deep packet inspection systems.
Anti-Censorship Technology Overview
| Technology | Purpose |
|---|---|
| Stealth Protocol | Masks VPN traffic to bypass detection |
| DPI Resistance | Avoids deep packet inspection filtering |
| Streaming Unblocking Rate | 100% success rate in testing |
| Censorship Circumvention | Effective in restrictive networks |
These capabilities make Proton VPN a preferred option for users operating in regions with high levels of internet censorship.
Pricing Structure and Subscription Plans
Proton VPN provides both free and premium subscription tiers, making it accessible to a broad range of users. The free version offers limited features but maintains the same privacy protections as the paid plans.
Proton VPN Pricing Comparison
| Plan Type | Two-Year Monthly Cost | One-Year Monthly Cost | Monthly Plan Cost |
|---|---|---|---|
| Free Plan | $0.00 | $0.00 | $0.00 |
| Paid Plan | $2.99 | $4.32 | $9.99 |
The free tier is particularly notable because it provides strong privacy protection without requiring payment, which is uncommon in the VPN industry.
Independent Security Audits and Privacy Verification
Proton VPN has reinforced its privacy claims through multiple independent security audits. The service has been audited three separate times by the cybersecurity auditing firm Securitum.
These audits examined Proton VPN’s server infrastructure, application security, and no-logs policy to ensure compliance with the company’s public privacy commitments.
Privacy Audit Verification Matrix
| Audit Attribute | Details |
|---|---|
| Independent Auditor | Securitum |
| Total Audits Completed | Three separate audits |
| Audit Scope | Infrastructure, application security |
| Policy Verified | Strict no-logs policy |
| Legal Validation | Court-tested privacy framework |
Independent verification is essential in the VPN industry because it provides external validation that a provider does not secretly retain user activity logs.
Proton VPN’s Position Among the Top VPN Services in 2026
In the broader comparison of the top VPN providers worldwide in 2026, Proton VPN occupies a distinctive position as the leading transparency-focused VPN service. While many competitors emphasize speed or low-cost pricing, Proton VPN’s reputation is built on privacy engineering, open-source accountability, and advanced security infrastructure.
Its combination of Swiss jurisdiction, Secure Core multi-hop routing, open-source applications, and strong censorship circumvention technology makes it particularly appealing for users who demand maximum privacy and security from their VPN provider.
For privacy purists, security researchers, journalists, and advanced users seeking a deeply transparent VPN platform, Proton VPN continues to represent one of the most trusted solutions in the global VPN market.
4. ExpressVPN
Within the competitive ecosystem of the top VPN services in 2026, ExpressVPN continues to maintain a strong reputation as one of the most polished and user-friendly virtual private network providers available. While many VPN platforms prioritize complex security customization or aggressive pricing strategies, ExpressVPN has historically focused on simplicity, reliability, and consistent performance.
This positioning has made the service particularly appealing to beginners, casual users, and individuals who want a VPN solution that works immediately without requiring technical configuration. The provider often describes its platform as a “set-and-forget” VPN, meaning users can activate the service once and rely on it to automatically maintain privacy and secure connections across devices.
Headquartered in the British Virgin Islands, ExpressVPN benefits from a privacy-friendly jurisdiction that lies outside major international surveillance alliances such as the Five Eyes and Fourteen Eyes intelligence-sharing networks. This legal environment helps reinforce its strict no-logs policy and enhances trust among privacy-conscious users.
Infrastructure and Global Server Coverage
By 2026, ExpressVPN has continued to expand its global infrastructure to ensure reliable connectivity for users across multiple continents. The service now supports server coverage in approximately 105 countries, allowing users to access geographically diverse IP addresses and maintain stable connections from almost anywhere in the world.
Although ExpressVPN does not publicly disclose its exact server count in the same way some competitors do, the company focuses heavily on server quality, optimized routing, and secure hardware environments rather than sheer quantity.
ExpressVPN Infrastructure Overview
| Infrastructure Category | Specification Description |
|---|---|
| Company Headquarters | British Virgin Islands |
| Server Country Coverage | 105 countries |
| Maximum Simultaneous Devices | 14 devices |
| Server Architecture | TrustedServer RAM-only infrastructure |
| VPN Protocol Technology | Lightway and Lightway Turbo |
| Data Logging Policy | Strict no-logs policy |
The broad geographic distribution ensures low-latency connections while allowing users to bypass region-based restrictions on digital content platforms.
Lightway Turbo Protocol and Network Performance
One of ExpressVPN’s key technological innovations is its proprietary Lightway protocol. Originally designed to compete with modern VPN tunneling technologies such as WireGuard, the Lightway protocol emphasizes speed, fast reconnections, and efficient battery consumption on mobile devices.
In 2026, ExpressVPN introduced an enhanced version known as Lightway Turbo. This updated protocol further improves network performance through optimized routing and reduced connection overhead.
Independent performance tests conducted on a standard 100 Mbps internet connection recorded impressive download speeds using Lightway Turbo.
Performance Benchmark Matrix
| Performance Metric | Observed Result |
|---|---|
| Test Connection Speed | 100 Mbps |
| Recorded Download Speed | 98 Mbps |
| Speed Loss | 2% |
| Average Latency | 2 milliseconds |
| Connection Stability | Very High |
| Streaming Performance | Ultra HD / 4K |
These results demonstrate that ExpressVPN continues to rank among the fastest VPN services available, even while prioritizing user-friendly configuration and minimal setup complexity.
TrustedServer Technology and RAM-Only Security
One of ExpressVPN’s defining security innovations is its TrustedServer infrastructure. Unlike traditional servers that store data on permanent hard drives, TrustedServer operates entirely on volatile RAM memory.
RAM-based servers automatically erase all stored data whenever the system reboots or powers down. This design ensures that no historical data can remain on the server hardware.
TrustedServer Security Architecture
| Server Feature | Security Function |
|---|---|
| RAM-only infrastructure | Prevents permanent data storage |
| Automatic data wipe | All data deleted on every reboot |
| Hardened operating environment | Reduces risk of server compromise |
| Secure server provisioning | Centralized management of server configurations |
| Consistent server software | Ensures uniform security across the global network |
This server model has become increasingly influential across the VPN industry, with many competitors adopting similar diskless architectures.
Core Technical Specifications
ExpressVPN integrates several advanced networking technologies to maintain a balance between strong encryption and user-friendly performance.
Encryption and Protocol Specifications
| Technology Category | Implementation Details |
|---|---|
| Primary Encryption | AES-256-GCM |
| VPN Protocols Supported | Lightway, OpenVPN, IKEv2 |
| Data Authentication | SHA-512 HMAC |
| Perfect Forward Secrecy | Enabled across sessions |
| DNS Leak Protection | Built-in private DNS infrastructure |
| Network Kill Switch | Automatic connection shutdown during VPN interruption |
These security features ensure that user data remains encrypted and protected from interception while maintaining high network efficiency.
Streaming Compatibility and Content Access
One of the major use cases for VPN services is accessing region-restricted streaming content. ExpressVPN has historically performed well in this area, maintaining compatibility with a wide range of streaming platforms.
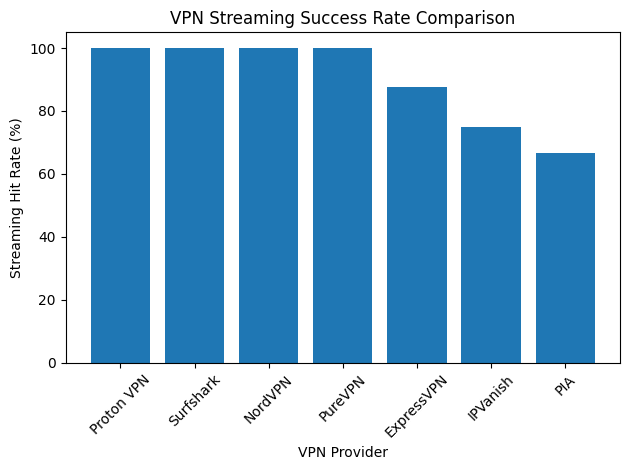
However, testing conducted in December 2025 revealed that the service temporarily failed to unblock the United Kingdom library of Netflix. Despite this isolated limitation, ExpressVPN continues to maintain strong overall streaming compatibility.
Streaming Platform Access Performance
| Streaming Metric | Performance Result |
|---|---|
| Overall Streaming Hit Rate | 87.5% |
| 4K Streaming Capability | Fully supported |
| Streaming Platform Compatibility | Multiple major platforms |
| Netflix UK Access | Failed in December 2025 testing |
Despite occasional service fluctuations, ExpressVPN remains a strong option for users seeking reliable streaming performance combined with privacy protection.
Device Compatibility and Ease of Use
One of ExpressVPN’s greatest strengths lies in its exceptionally intuitive user interface. The software is designed to allow users to connect to a VPN server with a single click, eliminating the complexity often associated with network configuration.
The service also supports a wide range of platforms including:
• Windows
• macOS
• Linux
• Android
• iOS
• Smart TVs
• Gaming consoles (via router setup)
ExpressVPN Device Support Overview
| Device Category | Compatibility Level |
|---|---|
| Desktop Computers | Full application support |
| Smartphones and Tablets | Dedicated mobile apps |
| Smart TVs | Supported through native apps |
| Gaming Consoles | Router-based configuration |
| Routers | Custom firmware available |
The ability to install ExpressVPN directly on routers allows users to protect entire home networks without configuring each device individually.
Pricing Structure and Subscription Model
ExpressVPN traditionally occupied the premium pricing segment of the VPN market. However, in 2026 the company adjusted its pricing model to become more competitive with other leading providers.
The new subscription structure includes extended multi-year plans that significantly reduce the monthly cost.
ExpressVPN Pricing Overview
| Plan Type | Monthly Cost Estimate |
|---|---|
| 28-Month Subscription Plan | $2.44 per month |
| Annual Plan | Higher than long-term plan |
| Monthly Plan | Premium pricing tier |
| Money-Back Guarantee | 30-day refund policy |
This updated pricing strategy reflects growing competition within the VPN industry, where long-term subscription discounts have become a standard marketing approach.
Independent Security Audits and Transparency
ExpressVPN has distinguished itself within the VPN industry through its extensive commitment to third-party security verification. The company has undergone more than 22 independent security audits performed by respected cybersecurity firms.
These audits examine multiple aspects of the service, including its server infrastructure, software security, encryption protocols, and privacy policies.
Independent Audit Verification Matrix
| Audit Attribute | Details |
|---|---|
| Total Independent Audits | 22+ completed audits |
| Audit Focus Areas | Infrastructure, privacy, application code |
| Privacy Policy Verified | Strict no-logs policy |
| Server Technology Examined | TrustedServer architecture |
| External Security Firms | Multiple cybersecurity auditors |
Regular independent auditing has become a major trust signal in the VPN industry, and ExpressVPN’s extensive audit history places it among the most thoroughly examined providers.
ExpressVPN’s Position Among the Top VPN Providers in 2026
Within the broader comparison of the top VPN services worldwide in 2026, ExpressVPN maintains a unique position as one of the most polished and accessible VPN platforms. While some competitors focus on ultra-low pricing or highly customizable technical features, ExpressVPN prioritizes simplicity, reliability, and seamless user experience.
Its combination of RAM-only server infrastructure, high-performance Lightway Turbo protocol, broad global coverage, and extensive security auditing makes it an attractive choice for users who want a dependable VPN solution without complicated configuration.
For beginners, households, and users seeking a VPN that operates reliably with minimal manual setup, ExpressVPN continues to represent one of the most refined and user-friendly options in the global VPN market.
5. Private Internet Access (PIA)
Among the major VPN providers operating globally in 2026, Private Internet Access (PIA) has built a reputation as one of the most customizable and technically flexible services available. While many VPN companies focus on simplified interfaces or bundled security features, PIA distinguishes itself by offering deep configuration options that appeal to advanced users, developers, and network enthusiasts.
This emphasis on customization has made Private Internet Access a preferred solution for users who want detailed control over their encryption settings, connection protocols, port forwarding configurations, and network routing behaviors. The service is particularly attractive to power users who prefer tailoring their VPN setup to specific performance, privacy, or networking requirements.
Despite being headquartered in the United States, a jurisdiction often criticized for extensive surveillance laws, PIA has repeatedly demonstrated the effectiveness of its no-logs policy. The company has twice been involved in legal proceedings where it was unable to provide user activity logs because such data was never collected or stored in the first place. These legal outcomes have reinforced confidence in the provider’s privacy claims.
Global Infrastructure and Network Scale
One of the most remarkable aspects of Private Internet Access is the sheer size of its server network. While many VPN providers operate several thousand servers globally, PIA’s infrastructure is estimated to include up to 35,000 servers distributed across 91 countries.
The extensive server coverage enables improved load balancing, faster connection speeds, and greater geographic flexibility for users who need access to region-specific IP addresses.
A particularly unique feature of the PIA network is its comprehensive coverage within the United States. The provider operates servers in every single U.S. state, making it one of the only VPN services capable of offering state-level IP selection.
PIA Global Infrastructure Overview
| Infrastructure Category | Specification Description |
|---|---|
| Estimated Total Servers | Up to 35,000 servers |
| Countries Covered | 91 countries |
| U.S. Server Coverage | Servers available in all 50 states |
| Server Infrastructure | Large-scale distributed architecture |
| VPN Protocol Support | WireGuard, OpenVPN |
| Jurisdiction | United States |
| Privacy Policy | Court-proven no-logs policy |
This nationwide server distribution provides a unique advantage for users attempting to access services restricted to specific states, such as regional sports broadcasts or localized online platforms.
Performance and Speed Benchmarks
Although Private Internet Access is known primarily for its customization capabilities rather than raw speed performance, it still delivers competitive network speeds in real-world testing scenarios.
Recent performance benchmarks show that PIA maintains a speed retention score of approximately 86.8 percent. This means that most users experience minimal bandwidth loss when connected to the VPN.
Network Performance Benchmark Matrix
| Performance Metric | Observed Result |
|---|---|
| Average Speed Retention | 86.8% |
| Connection Stability | High |
| Protocol Performance | WireGuard optimized |
| Streaming Compatibility | Moderate |
| Gaming Suitability | Good |
While slightly lower than some of the fastest competitors such as NordVPN or Surfshark, these speeds remain more than adequate for browsing, gaming, video streaming, and file transfers.
Advanced Customization and User Control
The defining characteristic of Private Internet Access is its deep configuration flexibility. The application interface allows users to modify numerous aspects of the VPN connection, enabling highly personalized network behavior.
This level of customization is rarely matched by other VPN providers, which often prioritize simplicity over advanced configuration.
Advanced Configuration Options
| Customization Feature | Functional Benefit |
|---|---|
| Encryption Level Selection | Allows users to balance speed and security |
| Custom DNS Configuration | Enables use of private or third-party DNS servers |
| Port Forwarding Support | Improves connectivity for torrenting and gaming |
| Split Tunneling | Routes selected applications outside the VPN tunnel |
| Protocol Selection | Choice between WireGuard and OpenVPN |
| Connection Automation | Auto-connect rules for trusted or public networks |
These capabilities make PIA particularly appealing for users who want granular control over their privacy and performance settings.
Open-Source Software Transparency
Private Internet Access also stands out as one of the few major VPN providers that maintains fully open-source applications. All major PIA client software is publicly available for inspection, allowing independent developers and cybersecurity experts to review the code.
Open-source software improves transparency and allows the broader security community to verify the integrity of the VPN client.
Transparency and Security Verification
| Transparency Feature | Implementation Details |
|---|---|
| Open-Source Applications | Full public access to application source code |
| Community Code Audits | Security researchers can independently review code |
| Privacy Documentation | Public disclosure of logging practices |
| Security Updates | Regular software updates and patches |
This approach significantly increases trust among technically inclined users who prefer verifiable privacy practices rather than proprietary software systems.
MACE Ad-Blocking and Threat Protection
Private Internet Access includes a built-in security feature known as MACE. This system functions as a DNS-based ad and malware blocker that filters out unwanted domains before they can load within a browser or application.
MACE helps prevent exposure to malicious advertisements, trackers, and pop-up malware.
Security Feature Overview
| Security Tool | Functional Description |
|---|---|
| MACE Ad Blocker | Blocks advertising networks and tracking domains |
| Malware Domain Filtering | Prevents access to known malicious websites |
| Tracker Protection | Reduces data collection by third-party advertisers |
| DNS Leak Protection | Ensures browsing queries remain within encrypted tunnels |
| Kill Switch | Stops internet traffic if the VPN connection drops |
These security mechanisms improve browsing safety and reduce exposure to intrusive advertising networks.
Streaming and Entertainment Performance
Although Private Internet Access performs well in many networking scenarios, it is generally considered less reliable for streaming platform unblocking compared with some competitors.
Testing indicates that the service achieves an average streaming compatibility rate of approximately 66.67 percent.
Streaming Performance Overview
| Streaming Metric | Performance Result |
|---|---|
| Overall Streaming Hit Rate | 66.67% |
| High-Definition Streaming | Supported |
| Platform Compatibility | Moderate |
| Regional Content Access | Variable depending on server |
This means that while PIA can access many streaming services, it is not always as consistent as VPN providers specifically optimized for entertainment platforms.
Pricing Structure and Subscription Options
Private Internet Access follows a straightforward pricing model with significant discounts available for long-term subscription commitments. Its long-term plans position it as one of the more affordable premium VPN services on the market.
PIA Pricing Structure
| Subscription Tier | Effective Monthly Cost | Renewal Frequency |
|---|---|---|
| One-Month Plan | $11.95 | Monthly |
| One-Year Plan | $3.33 | Annual |
| Three-Year + 3 Months Plan | $2.03 | Every three years |
These long-term plans offer substantial cost savings, making PIA attractive to users seeking powerful customization features at a relatively low price.
Privacy Verification and Legal Validation
Despite operating from the United States, Private Internet Access has reinforced its credibility through legal validation of its no-logs policy. In two separate court cases, the company was unable to provide user activity records because it did not store any.
Privacy Verification Summary
| Verification Attribute | Details |
|---|---|
| Jurisdiction | United States |
| Legal Validation | No-logs policy proven in court |
| Number of Legal Cases | Two cases confirming absence of logs |
| Logging Practices | No user activity tracking |
| Software Transparency | Fully open-source client applications |
These cases have become widely cited examples within the VPN industry demonstrating that strong privacy policies can remain effective even within jurisdictions known for strict data laws.
Private Internet Access in the Global VPN Rankings
Within the broader comparison of the top VPN services in 2026, Private Internet Access holds a distinct position as the leading customization-focused VPN provider. Its combination of massive server infrastructure, extensive configuration options, and open-source transparency makes it especially appealing for technically advanced users.
Although it may not match some competitors in streaming performance or beginner-friendly design, its flexibility and proven privacy record continue to make it a powerful choice for users who prioritize control, transparency, and network customization in their VPN experience.
6. CyberGhost
Within the competitive landscape of the top VPN providers in 2026, CyberGhost has established itself as a popular option for travelers, streaming enthusiasts, and beginner users seeking a straightforward and purpose-driven VPN experience. While some VPN providers emphasize highly technical features or advanced customization tools, CyberGhost focuses on usability, task-based server selection, and reliable access to streaming services.
The service has gained considerable traction among users who travel frequently or rely on VPN technology to access geographically restricted entertainment platforms. By organizing its servers according to specific use cases such as streaming, torrenting, and gaming, CyberGhost simplifies the connection process and reduces the technical knowledge required to select the best server for a particular activity.
CyberGhost is headquartered in Romania, a country known for its strong stance on digital privacy and its refusal to implement certain European data retention directives. This legal environment provides a supportive framework for the company’s strict no-logs policy and privacy-first infrastructure.
Global Server Infrastructure and Geographic Coverage
CyberGhost operates one of the largest VPN server networks in the industry. By 2026, the provider maintains more than 11,690 servers distributed across approximately 100 countries. This large-scale infrastructure allows CyberGhost to offer a wide selection of connection points while maintaining adequate bandwidth capacity for high-demand activities such as streaming and gaming.
Large networks also enable providers to balance traffic loads efficiently, which can improve overall performance and reduce connection congestion during peak usage hours.
CyberGhost Global Infrastructure Overview
| Infrastructure Category | Specification Description |
|---|---|
| Total Servers | 11,690+ servers |
| Countries Covered | 100 countries |
| Server Categories | Streaming, gaming, torrenting, standard browsing |
| Headquarters | Romania |
| Privacy Policy | Strict no-logs policy |
| Server Management | Combination of leased and owned infrastructure |
The wide geographic distribution enables users to connect to nearby servers for faster speeds or access distant servers to bypass region-based content restrictions.
Task-Based Server Optimization
One of CyberGhost’s defining features is its task-oriented server classification system. Instead of requiring users to manually search for the fastest or most suitable server, the platform organizes servers into categories based on their intended use.
For example, specific servers are optimized for streaming platforms such as Netflix or Hulu, while others are configured to deliver lower latency for gaming or high-speed file transfers.
Task-Based Server Categories
| Server Category | Optimized Use Case |
|---|---|
| Streaming Servers | Access to region-locked platforms such as Netflix and Hulu |
| Gaming Servers | Reduced latency and improved connection stability |
| Torrenting Servers | Optimized for peer-to-peer file sharing |
| Standard Servers | General browsing and everyday internet use |
This approach significantly simplifies the VPN selection process, making the service particularly attractive to beginners or users unfamiliar with networking concepts.
Performance and Speed Benchmarks
CyberGhost provides strong local performance when users connect to nearby servers. Tests conducted in 2026 show that local servers experience an average speed reduction of only about six percent compared with the user’s base internet connection.
However, performance may vary when connecting to geographically distant servers, where speed reductions can become more noticeable.
CyberGhost Performance Benchmark Matrix
| Performance Metric | Observed Result |
|---|---|
| Starting Subscription Price | $2.19 per month |
| Download Speed Loss (Local) | 6% |
| Average Latency | 4 milliseconds |
| Maximum Device Connections | 7 devices |
| Long-Distance Speed Reduction | Approximately 19% |
While these figures remain competitive within the industry, they indicate that CyberGhost may experience slightly greater performance degradation on distant servers compared with some premium competitors.
Security Infrastructure and NoSpy Servers
CyberGhost provides an additional layer of privacy through its proprietary NoSpy server infrastructure. These servers are physically located within the company’s Romanian headquarters and are operated exclusively by CyberGhost staff rather than third-party data center operators.
This approach reduces the risk of external interference and ensures that the entire server environment remains under direct company control.
NoSpy Server Security Architecture
| Security Component | Functional Benefit |
|---|---|
| Dedicated NoSpy Servers | Managed exclusively by CyberGhost personnel |
| Physical Data Center Security | Servers housed in controlled Romanian facilities |
| Restricted Access Infrastructure | Limited external administrative access |
| Independent Server Management | Reduced reliance on third-party hosting providers |
By maintaining physical control over these servers, CyberGhost strengthens the overall integrity of its privacy infrastructure.
Streaming Performance and Entertainment Access
CyberGhost has positioned itself as one of the most reliable VPN providers for streaming access. Its dedicated streaming server category simplifies the process of accessing content libraries that are typically restricted by geographic location.
These servers are regularly updated and optimized to maintain compatibility with popular streaming platforms.
Streaming Performance Overview
| Streaming Metric | Performance Result |
|---|---|
| Streaming Server Optimization | Dedicated platform servers |
| Ultra HD Streaming | Supported |
| Platform Compatibility | Multiple streaming services |
| Server Selection Method | Pre-configured streaming servers |
This task-oriented approach significantly improves usability for users who want to bypass geographic restrictions without needing to test multiple servers manually.
Device Compatibility and User Accessibility
CyberGhost’s software ecosystem is designed with accessibility and simplicity in mind. The user interface provides a streamlined connection process and clearly labeled server categories, allowing users to select the most appropriate server with minimal effort.
CyberGhost Device Compatibility Matrix
| Device Category | Compatibility Level |
|---|---|
| Desktop Computers | Windows, macOS, Linux |
| Mobile Devices | Android and iOS applications |
| Smart TVs | Supported via app or router |
| Routers | Manual configuration supported |
| Browser Extensions | Available for major browsers |
The platform allows up to seven simultaneous device connections, which is sufficient for most households or small teams.
Pricing Structure and Consumer Protection
CyberGhost has positioned itself as a competitively priced VPN service, particularly when users select long-term subscription plans. The provider also offers one of the longest refund periods in the industry.
CyberGhost Pricing Overview
| Pricing Attribute | Details |
|---|---|
| Starting Price | $2.19 per month |
| Maximum Device Connections | 7 devices |
| Refund Policy | 45-day money-back guarantee |
| Long-Term Discounts | Available for multi-year plans |
The 45-day money-back guarantee is notably longer than the standard 30-day refund window offered by most VPN providers, providing additional consumer protection.
Comparison of Global Performance Variability
While CyberGhost performs very well on nearby servers, some testing indicates that its long-distance server performance may decline more noticeably than that of certain competitors.
Global Performance Comparison
| VPN Provider | Local Speed Loss | Long-Distance Speed Loss |
|---|---|---|
| CyberGhost | 6% | 19% |
| NordVPN | Lower local loss | Approximately 14% |
This difference does not necessarily affect everyday browsing but may become noticeable when connecting to servers located on distant continents.
CyberGhost’s Position Among the Top VPN Services in 2026
Within the broader ranking of the top VPN providers in 2026, CyberGhost occupies a distinct position as a streaming-focused and traveler-friendly VPN service. Its large server network, specialized streaming infrastructure, and simplified server selection system make it particularly appealing for users seeking an accessible and entertainment-oriented VPN platform.
While some competitors may offer slightly stronger long-distance performance or advanced configuration tools, CyberGhost’s emphasis on ease of use, dedicated streaming servers, and privacy-focused infrastructure ensures that it remains one of the most practical VPN solutions for everyday users and international travelers.
7. IPVanish
Among the top VPN providers operating in 2026, IPVanish has built a strong reputation as a performance-focused VPN service designed for users who prioritize raw connection speed and broad device compatibility. While many VPN providers emphasize security bundles or entertainment streaming capabilities, IPVanish has historically focused on delivering fast throughput, reliable infrastructure, and unrestricted device coverage.
This emphasis on speed and infrastructure control has made IPVanish particularly popular among heavy downloaders, online gamers, and users managing large numbers of connected devices. One of the service’s most attractive features is its support for unlimited simultaneous device connections, allowing subscribers to secure every device within a household or small business network using a single account.
IPVanish operates from the United States and differentiates itself by owning and managing its own server infrastructure rather than relying heavily on third-party hosting providers. This operational model gives the company greater control over hardware performance, network routing, and server maintenance.
Global Infrastructure and Network Control
Although IPVanish operates a smaller number of servers than some of the largest VPN providers, the company focuses heavily on infrastructure quality and network management. By maintaining direct control over its servers, IPVanish can optimize performance and ensure consistent service reliability.
As of 2026, the service operates more than 2,400 servers distributed across 108 countries. This international network enables users to access geographically diverse IP addresses while maintaining stable connection speeds.
IPVanish Infrastructure Overview
| Infrastructure Category | Specification Description |
|---|---|
| Total Servers | 2,400+ servers |
| Countries Covered | 108 countries |
| Server Ownership Model | Company-managed infrastructure |
| Device Connection Limit | Unlimited devices |
| Headquarters | United States |
| VPN Protocol Support | WireGuard, OpenVPN, IKEv2 |
| Privacy Policy | Verified no-logs policy |
The ownership of its physical infrastructure allows IPVanish to maintain tighter control over server performance and security standards.
Speed Performance and Benchmark Results
One of IPVanish’s most notable strengths is its exceptional speed performance. Independent performance testing conducted in 2026 placed IPVanish among the fastest VPN services available, with the highest download retention score in its category.
These speed advantages are largely attributed to the company’s direct server management and efficient routing infrastructure.
IPVanish Performance Benchmark Matrix
| Performance Metric | Observed Result |
|---|---|
| Average Download Retention | 90.1% |
| Local Download Speed | 96 Mbps |
| Speed Loss | 4% |
| Average Ping Latency | 3 milliseconds |
| Server Network Coverage | 108 countries |
| Starting Subscription Price | $2.19 per month |
These results indicate that IPVanish is particularly well suited for high-bandwidth activities such as gaming, torrenting, large file transfers, and high-definition streaming.
Infrastructure Ownership and Network Efficiency
A key factor behind IPVanish’s performance advantage is its infrastructure ownership model. Many VPN providers lease servers from third-party data centers, which can introduce additional network overhead and limit optimization capabilities.
IPVanish instead manages much of its hardware directly, enabling faster network routing and improved throughput.
Infrastructure Management Advantages
| Infrastructure Feature | Functional Benefit |
|---|---|
| Self-Owned Servers | Greater control over performance and security |
| Direct Network Routing | Reduced dependency on external providers |
| Optimized Bandwidth Allocation | Improved speed consistency during peak traffic periods |
| Centralized Infrastructure Control | Faster updates and maintenance deployment |
This approach helps ensure that IPVanish maintains stable performance even during periods of heavy network demand.
Device Compatibility and Unlimited Connections
Another major advantage of IPVanish is its support for unlimited simultaneous device connections. Many VPN providers limit the number of devices that can be connected under a single subscription, often ranging between five and ten devices.
IPVanish removes this limitation entirely, allowing users to secure an unlimited number of devices without purchasing additional subscriptions.
Device Compatibility Overview
| Device Category | Compatibility Level |
|---|---|
| Desktop Computers | Windows, macOS, Linux |
| Mobile Devices | Android and iOS applications |
| Smart TVs | Supported through manual setup |
| Routers | Router-level installation |
| Gaming Consoles | Protected through router VPN |
This unlimited device policy makes IPVanish especially attractive for large households or environments with many connected devices.
Security Architecture and Encryption Standards
IPVanish integrates strong encryption technologies and modern VPN protocols to ensure that user traffic remains secure while maintaining high connection speeds.
Encryption and Security Framework
| Security Technology | Implementation Details |
|---|---|
| Encryption Standard | AES-256 encryption |
| VPN Protocols | WireGuard, OpenVPN, IKEv2 |
| DNS Leak Protection | Built-in DNS security |
| Kill Switch | Automatic internet shutdown during connection loss |
| Traffic Obfuscation | Optional scrambling for restrictive networks |
These technologies ensure that user data remains encrypted and protected against interception while traveling through public networks.
Streaming Compatibility and Entertainment Access
While IPVanish performs exceptionally well in terms of speed, its streaming compatibility has historically been less consistent than some competitors that specifically optimize for entertainment platforms.
Recent testing results indicate that the service successfully accesses many streaming services but may occasionally encounter compatibility issues with certain regional libraries.
Streaming Performance Overview
| Streaming Metric | Performance Result |
|---|---|
| Overall Streaming Hit Rate | 75% |
| High-Definition Streaming | Supported |
| Platform Compatibility | Moderate |
| Streaming Optimization Servers | Not specialized |
Although not the most reliable option for streaming enthusiasts, IPVanish still performs adequately for many entertainment services.
Pricing Structure and Subscription Options
IPVanish has adopted a competitive pricing strategy designed to attract long-term subscribers while maintaining affordable entry points for new users.
IPVanish Pricing Overview
| Pricing Attribute | Details |
|---|---|
| Starting Monthly Price | $2.19 per month |
| Device Connection Limit | Unlimited devices |
| Refund Policy | 30-day money-back guarantee |
| Long-Term Plan Discounts | Available for extended plans |
The combination of competitive pricing and unlimited device support makes IPVanish an attractive option for households with many connected devices.
Independent Security Audits and Privacy Verification
Operating within the United States raises privacy concerns for some users due to the country’s surveillance laws. To address these concerns, IPVanish has undergone independent security audits designed to verify its no-logs policy.
Two respected cybersecurity firms, Leviathan Security Group and Schellman Compliance, have examined IPVanish’s infrastructure and privacy practices.
Privacy Verification Matrix
| Audit Attribute | Details |
|---|---|
| Independent Auditors | Leviathan Security Group, Schellman |
| Audit Focus | Infrastructure security and logging |
| Policy Verified | Strict no-logs policy |
| Logging Practices | No user activity storage |
These audits help reinforce the company’s commitment to protecting user privacy despite its jurisdiction.
IPVanish’s Position Among the Top VPN Services in 2026
Within the global ranking of the top VPN providers in 2026, IPVanish occupies a distinct niche as a performance-focused VPN optimized for speed and device scalability. Its high download retention scores, unlimited device connections, and self-managed infrastructure make it particularly appealing for users who prioritize throughput and reliability.
While some competitors offer stronger streaming compatibility or advanced privacy jurisdictions, IPVanish continues to excel in raw performance and network efficiency. For gamers, large households, and heavy internet users who require maximum connection speeds across many devices, IPVanish remains one of the most capable VPN solutions available in the modern VPN market.
8. Mullvad VPN
Within the competitive ecosystem of global VPN providers in 2026, Mullvad VPN continues to occupy a distinctive position as one of the most privacy-focused and anonymity-oriented services available. Unlike many commercial VPN providers that emphasize entertainment access, aggressive marketing promotions, or bundled cybersecurity tools, Mullvad has built its reputation almost entirely around transparency, minimal data collection, and strict privacy protections.
For privacy advocates, cybersecurity researchers, journalists, and individuals concerned about surveillance or digital tracking, Mullvad is frequently considered one of the most trustworthy VPN services in the industry. Its design philosophy prioritizes anonymity above convenience, which is reflected in how users create accounts, pay for subscriptions, and interact with the service.
Headquartered in Sweden, Mullvad operates within the European Union regulatory framework while maintaining a strict commitment to collecting as little user information as possible. The company’s policies intentionally avoid traditional account structures that require email addresses or personal data.
Anonymous Account Creation System
One of Mullvad’s most defining features is its unique account creation system. Unlike conventional VPN services that require an email address and user credentials, Mullvad assigns each user a randomly generated 16-digit account number.
This system eliminates the need to store personally identifiable information and significantly reduces the risk of user identification through account data.
Anonymous Account System Overview
| Account Feature | Implementation Details |
|---|---|
| Account Identifier | Randomly generated 16-digit number |
| Email Requirement | No email required |
| Personal Information | No personally identifiable information collected |
| Account Authentication | Account number used as login credential |
| Account Recovery | Controlled solely by possession of account number |
Because the system does not rely on traditional identity-based registration, Mullvad minimizes the amount of personal information stored within its infrastructure.
Flat Pricing Model and Subscription Transparency
Another major aspect of Mullvad’s philosophy is its straightforward pricing model. Unlike many VPN providers that offer heavily discounted long-term plans or complex promotional pricing structures, Mullvad maintains a simple flat-rate subscription cost.
Users pay the same monthly price regardless of how long they remain subscribed, eliminating the marketing strategies commonly used in the VPN industry.
Mullvad Pricing Structure
| Pricing Attribute | Details |
|---|---|
| Monthly Cost | €5 per month |
| Approximate USD Equivalent | $5.44 – $5.67 depending on exchange rate |
| Contract Requirements | No long-term contracts |
| Promotional Discounts | None |
| Billing Structure | Fixed monthly rate |
This transparent pricing structure is designed to reinforce trust by avoiding hidden renewal price increases or introductory discounts.
Anonymous Payment Options
Mullvad also provides several payment options that allow users to maintain financial anonymity if desired. In addition to traditional payment methods such as credit cards and bank transfers, the service accepts cryptocurrency and even physical cash payments sent through the mail.
This flexibility allows users to subscribe without leaving identifiable payment records.
Payment Methods Overview
| Payment Method | Privacy Characteristics |
|---|---|
| Cash Payments | Maximum anonymity when mailed to Mullvad headquarters |
| Cryptocurrency | Allows pseudonymous payment transactions |
| Credit Card | Standard online payment option |
| Bank Transfer | Supported for traditional financial transactions |
Few VPN providers support anonymous cash payments, making Mullvad particularly appealing for users seeking maximum privacy.
Network Infrastructure and Protocol Support
Although Mullvad does not operate the largest server network in the VPN industry, it focuses on maintaining secure and well-optimized infrastructure that prioritizes privacy and performance.
The service primarily relies on modern VPN protocols such as WireGuard and OpenVPN, both of which are widely regarded for their security and reliability.
Mullvad Technical Infrastructure Overview
| Technical Category | Implementation Details |
|---|---|
| VPN Protocols Supported | WireGuard, OpenVPN |
| Encryption Standards | AES-256 and modern cryptographic implementations |
| DNS Leak Protection | Built-in DNS security mechanisms |
| Logging Policy | Strict no-logs infrastructure |
| Privacy Architecture | Minimal data collection systems |
WireGuard support allows Mullvad to maintain efficient performance while preserving strong encryption standards.
Independent Security Audits and Transparency
Transparency is a central component of Mullvad’s credibility within the cybersecurity community. The company regularly subjects its infrastructure and software systems to independent security audits conducted by respected cybersecurity firms.
In January 2026, the German security firm X41 D-Sec conducted a detailed audit of Mullvad’s account and payment infrastructure.
Security Audit Findings Overview
| Audit Attribute | Details |
|---|---|
| Auditing Organization | X41 D-Sec |
| Audit Completion Date | January 2026 |
| System Examined | Account creation and payment API |
| Privacy Outcome | No compromise of user privacy or identity |
| Minor Findings | Voucher race condition vulnerability |
| Overall Impact | No data integrity or privacy risks identified |
Although minor technical issues were identified, the audit confirmed that none of the vulnerabilities affected user privacy or compromised the integrity of Mullvad’s anonymity systems.
Transparency and Open Security Practices
Mullvad is widely respected within the cybersecurity industry for its unusually transparent operational practices. The company regularly publishes security reports, audit findings, and infrastructure updates.
Transparency Practices Overview
| Transparency Feature | Implementation Details |
|---|---|
| Independent Security Audits | Regular third-party audits |
| Public Infrastructure Reports | Documentation of server architecture |
| Open Communication | Public disclosure of vulnerabilities and fixes |
| Minimal Data Collection | Strict policies preventing user tracking |
These practices have helped establish Mullvad as one of the most trusted VPN providers among privacy professionals.
Streaming Compatibility and Feature Limitations
While Mullvad excels in privacy protection and anonymity, it does not prioritize entertainment-related features. The service intentionally avoids implementing specialized streaming optimization technologies that some competitors use to bypass platform restrictions.
As a result, Mullvad can struggle to consistently access certain streaming services.
Streaming Performance Overview
| Streaming Metric | Performance Result |
|---|---|
| Streaming Platform Optimization | Limited |
| Netflix Compatibility | Often blocked |
| Streaming Server Categories | Not implemented |
| Focus Area | Privacy and anonymity rather than media access |
For users whose primary goal is accessing streaming platforms, other VPN providers may offer more reliable compatibility.
Mullvad’s Position Among the Top VPN Services in 2026
Within the broader ranking of the top VPN providers worldwide in 2026, Mullvad occupies a unique role as the industry’s anonymity benchmark. Its commitment to minimal data collection, anonymous account creation, and transparent operational practices distinguishes it from many commercial VPN services that emphasize convenience or entertainment.
Although it lacks certain consumer-oriented features such as streaming optimization or bundled cybersecurity tools, Mullvad remains one of the most trusted VPN providers for users who prioritize privacy above all else.
For individuals seeking the highest level of anonymity, including journalists, researchers, activists, and privacy advocates, Mullvad continues to represent one of the most principled and transparent VPN services available in the modern internet privacy ecosystem.
9. PureVPN
Among the many VPN providers operating in 2026, PureVPN has developed a distinctive position as a feature-rich and modular VPN service designed to accommodate a wide range of user requirements. While many competitors bundle most features into a single subscription tier, PureVPN differentiates itself by offering a customizable add-on system that allows subscribers to expand their VPN capabilities according to specific needs.
This flexible approach has made PureVPN particularly attractive for users who require specialized networking tools such as dedicated IP addresses, port forwarding capabilities, or residential IP access. Rather than forcing users to pay for features they may not use, the platform allows subscribers to selectively enable advanced functionality.
PureVPN operates from the British Virgin Islands, a jurisdiction commonly favored by privacy-focused companies due to its absence from major international intelligence-sharing alliances. The location provides a favorable regulatory environment for maintaining strict privacy policies and protecting user data.
Global Infrastructure and Network Reach
By 2026, PureVPN has expanded its global infrastructure significantly, offering a network of more than 6,000 servers located across over 65 countries. This large server fleet allows the service to maintain stable connections and support high-bandwidth activities such as video streaming, file downloads, and remote work.
A geographically diverse network also helps users bypass regional content restrictions and maintain lower latency connections when accessing distant servers.
PureVPN Infrastructure Overview
| Infrastructure Category | Specification Description |
|---|---|
| Total Servers | 6,000+ servers |
| Countries Covered | 65+ countries |
| Company Headquarters | British Virgin Islands |
| Server Distribution | Global multi-region coverage |
| VPN Protocol Support | WireGuard, OpenVPN, IKEv2 |
| Privacy Monitoring | Continuous independent auditing |
The extensive server infrastructure ensures that PureVPN users have access to multiple connection options depending on their location and performance needs.
Performance and Speed Benchmarks
Performance testing conducted in 2026 demonstrates that PureVPN delivers competitive speeds for everyday browsing, streaming, and downloading. The service achieved a download retention score of approximately 85.8 percent during recent benchmarking tests.
Although slightly lower than some of the fastest VPN providers, these results remain strong enough for most internet activities.
PureVPN Performance Benchmark Matrix
| Performance Metric | Observed Result |
|---|---|
| Average Download Retention | 85.8% |
| Streaming Compatibility | Very High |
| Global Server Network | 6,000+ nodes |
| Country Coverage | 65+ countries |
| Entry-Level Subscription Price | $2.15 per month |
These results demonstrate that PureVPN provides balanced performance suitable for both casual and advanced users.
Streaming Performance and Content Access
One of PureVPN’s strongest areas of performance is its ability to bypass regional streaming restrictions. Testing conducted in 2026 recorded a 100 percent success rate when attempting to unblock major streaming platforms.
Streaming services often deploy VPN detection technologies, making this level of compatibility particularly notable.
Streaming Performance Overview
| Streaming Metric | Performance Result |
|---|---|
| Streaming Unblocking Success | 100% in 2026 testing |
| Ultra HD Streaming | Supported |
| Platform Compatibility | Multiple global services |
| Streaming Server Optimization | Dedicated optimized servers |
This high streaming success rate makes PureVPN an attractive option for users seeking consistent access to geographically restricted media libraries.
Continuous Privacy Auditing and Transparency
PureVPN has attempted to strengthen its privacy reputation by implementing an “always-on” auditing system. Unlike periodic audits conducted every few years by some VPN providers, PureVPN maintains an ongoing independent verification process conducted by KPMG.
This auditing system continuously evaluates the company’s infrastructure and logging policies to ensure compliance with its privacy commitments.
Privacy Verification Overview
| Audit Attribute | Details |
|---|---|
| Independent Auditor | KPMG |
| Audit Model | Continuous “always-on” monitoring |
| Policy Verified | No-logs infrastructure |
| Infrastructure Examined | Server operations and logging systems |
This ongoing audit framework helps improve transparency and reinforces the company’s commitment to privacy protection.
Modular Add-On Feature System
PureVPN’s most distinctive characteristic is its modular feature architecture. Rather than bundling all advanced networking features into a single subscription plan, the platform allows users to add specific capabilities through optional add-ons.
This approach provides greater flexibility and allows users to tailor the VPN service to their exact needs.
PureVPN Add-On Services Overview
| Add-On Feature | Starting Monthly Cost | Functional Benefit |
|---|---|---|
| Dedicated IP Address | $2.49 | Provides a static IP address for consistent access |
| Port Forwarding | $1.49 | Enables direct inbound connections for apps |
| Multi-Login Support | $1.49 | Allows use on 50+ devices simultaneously |
| Residential Network Access | $12.49 | Provides genuine residential IP addresses |
This flexible add-on system allows users to build a customized VPN environment tailored to their networking requirements.
Dedicated IP and Residential Network Capabilities
Two of the most notable add-on features offered by PureVPN are dedicated IP addresses and residential network access. These features are particularly useful for users who require stable, authentic IP addresses that appear similar to standard residential internet connections.
Dedicated and residential IPs can help reduce the likelihood of service blocks from websites that restrict VPN traffic.
Advanced Networking Feature Matrix
| Feature Type | Functional Advantage |
|---|---|
| Dedicated IP Address | Maintains consistent IP identity for online services |
| Residential IP Network | Mimics authentic home internet connections |
| Port Forwarding | Improves connectivity for peer-to-peer applications |
| Multi-Login Expansion | Supports large numbers of connected devices |
These specialized capabilities make PureVPN particularly useful for users with advanced networking requirements.
Device Compatibility and Multi-Platform Support
PureVPN supports a wide range of devices and operating systems, ensuring compatibility across both desktop and mobile environments.
Device Compatibility Overview
| Device Category | Compatibility Level |
|---|---|
| Desktop Platforms | Windows, macOS, Linux |
| Mobile Devices | Android and iOS applications |
| Smart TVs | Supported via apps and routers |
| Routers | Manual configuration supported |
| Browser Extensions | Available for major browsers |
This cross-platform compatibility allows users to protect multiple devices within a single ecosystem.
Pricing Structure and Accessibility
PureVPN’s base subscription plan is competitively priced, making it accessible for users who want entry-level VPN functionality without paying premium subscription rates.
PureVPN Pricing Overview
| Pricing Attribute | Details |
|---|---|
| Starting Monthly Price | $2.15 per month |
| Add-On Customization | Optional modular upgrades |
| Refund Policy | 31-day money-back guarantee |
| Long-Term Discount Plans | Available for extended plans |
The combination of low base pricing and optional feature upgrades makes PureVPN one of the most flexible pricing models in the VPN market.
PureVPN’s Position Among the Top VPN Services in 2026
Within the broader ranking of the top VPN providers worldwide in 2026, PureVPN stands out as the most modular and customizable service in terms of feature expansion. Its flexible add-on architecture, extensive server network, and strong streaming performance make it particularly attractive for users who require specific networking tools.
While some VPN providers focus exclusively on privacy features or streaming compatibility, PureVPN attempts to bridge both categories by offering strong entertainment access alongside optional advanced networking capabilities.
For users seeking an affordable VPN service with the ability to add specialized features such as dedicated IP addresses, port forwarding, or residential IP access, PureVPN remains one of the most versatile VPN solutions available in the modern internet privacy market.
10. Windscribe
Within the evolving ecosystem of virtual private network providers in 2026, Windscribe has built a strong reputation as a highly customizable and privacy-conscious VPN service with a particular focus on advanced ad-blocking capabilities and flexible user control. While many VPN services emphasize large server fleets or bundled cybersecurity features, Windscribe distinguishes itself through its powerful browser extensions, extensive configuration options, and sophisticated domain-blocking system.
Headquartered in Canada, Windscribe operates within a country that participates in international intelligence-sharing alliances. However, the company has historically emphasized transparency and user privacy through minimal logging practices and strong encryption protocols. Windscribe has gained popularity among technically inclined users who want granular control over how their VPN connection operates.
One of the platform’s defining characteristics is its advanced network filtering system known as R.O.B.E.R.T., which allows users to customize how advertisements, trackers, malware domains, and other unwanted online content are blocked.
Global Infrastructure and Network Coverage
Windscribe maintains a globally distributed server infrastructure designed to provide reliable connections for both free and paid users. Although its network is smaller than some of the largest VPN providers, it focuses on performance optimization and efficient bandwidth management.
The service also provides users with access to both dynamic and shared static IP addresses depending on subscription preferences.
Windscribe Infrastructure Overview
| Infrastructure Category | Specification Description |
|---|---|
| Company Headquarters | Canada |
| Server Network Coverage | Global distributed server network |
| Device Connection Limit | Unlimited simultaneous connections |
| Static IP Availability | Shared static IP options available |
| VPN Protocol Support | WireGuard, OpenVPN, IKEv2 |
| Privacy Policy | Verified no-logs policy |
This infrastructure allows Windscribe users to maintain stable connections across multiple devices without the limitations often imposed by competing VPN services.
Performance and Speed Benchmarks
Despite its emphasis on customization features and browser-based privacy tools, Windscribe still delivers strong network performance. Benchmark tests conducted in recent evaluations indicate that the service can achieve download speeds of approximately 96 Mbps on a standard 100 Mbps connection.
Latency performance also remains very competitive, making the service suitable for gaming and real-time communications.
Windscribe Performance Benchmark Matrix
| Performance Metric | Observed Result |
|---|---|
| Local Download Speed | 96 Mbps |
| Speed Loss | Approximately 4% |
| Average Latency | 3 milliseconds |
| Connection Stability | High |
| Gaming Performance | Suitable for low-latency applications |
These performance figures place Windscribe among the faster VPN providers in terms of raw connection speed.
R.O.B.E.R.T. Ad-Blocking and Network Filtering System
Windscribe’s most well-known feature is its advanced filtering system called R.O.B.E.R.T. This technology functions as a DNS-level filtering engine that blocks unwanted domains before they load within the user’s browser or applications.
Unlike basic ad blockers that only target advertising networks, R.O.B.E.R.T. allows users to customize multiple categories of blocked content.
R.O.B.E.R.T. Filtering Capabilities
| Blocking Category | Functional Benefit |
|---|---|
| Advertising Networks | Prevents intrusive advertisements |
| Tracking Domains | Blocks behavioral tracking and analytics scripts |
| Malware Domains | Prevents access to known malicious websites |
| Social Media Trackers | Reduces cross-platform behavioral monitoring |
| Custom Domain Lists | Allows users to manually define blocked domains |
Users can enable different blocking tiers depending on their preferred balance between privacy protection and website functionality.
Browser Extension Integration
Windscribe is widely recognized for offering one of the most powerful VPN browser extensions available. The browser extension operates as more than a simple proxy and includes several privacy-enhancing features.
Browser Extension Features
| Feature Category | Functional Benefit |
|---|---|
| Browser-Based VPN Routing | Encrypts browser traffic independently |
| Cookie Management | Automatically removes tracking cookies |
| Time-Zone Spoofing | Prevents browser fingerprinting techniques |
| WebRTC Leak Prevention | Protects real IP address within browsers |
| Integrated R.O.B.E.R.T. Control | Allows filtering directly within the browser interface |
These tools make Windscribe particularly effective for users who want browser-level privacy controls without configuring system-wide VPN settings.
Free Tier and Accessibility
One of Windscribe’s most appealing aspects is its generous free tier. The free plan provides users with up to 10 gigabytes of monthly data when using the standard configuration.
This data allowance is significantly larger than the free plans offered by many competing VPN providers.
Windscribe Free Plan Overview
| Feature Category | Free Tier Specification |
|---|---|
| Monthly Data Allowance | 10 GB |
| Device Limit | Unlimited devices |
| Server Locations | Limited selection |
| Ad-Blocking Features | R.O.B.E.R.T. included |
| Upgrade Availability | Full paid plan upgrade available |
The free plan allows users to experience most of the platform’s core functionality before committing to a paid subscription.
Static IP Options and Network Flexibility
Windscribe also offers shared static IP address options, which can be useful for users who require consistent IP identities for accessing certain services or maintaining stable connections.
Static IP Feature Overview
| Static IP Feature | Details |
|---|---|
| Static IP Availability | Shared static IP pools |
| Starting Price | From $2.00 per month |
| Use Cases | Remote work, secure account access |
| Geographic Availability | Limited to specific server regions |
These static IP addresses provide an alternative to constantly rotating dynamic IPs typically used by VPN services.
Pricing Structure and Subscription Plans
Windscribe’s paid subscription plan is competitively priced and provides access to the full network of servers and advanced customization features.
Windscribe Pricing Overview
| Pricing Attribute | Details |
|---|---|
| Free Plan | 10 GB monthly data |
| Paid Plan (Annual) | $5.75 per month |
| Device Connections | Unlimited devices |
| Feature Availability | Full access to R.O.B.E.R.T. tools |
This pricing structure offers a balance between affordability and powerful privacy functionality.
Privacy Verification and Legal Validation
Although Windscribe has not yet undergone a full organizational audit by one of the major global accounting firms often used by large VPN providers, the service has demonstrated its privacy claims through legal precedent.
In a 2023 court case in Greece, authorities attempted to obtain user activity data related to a server investigation. Windscribe was unable to provide any identifiable user data because it did not store such information.
Privacy Verification Overview
| Verification Attribute | Details |
|---|---|
| Jurisdiction | Canada |
| Legal Case | Greek court investigation (2023) |
| Outcome | No user logs available |
| Logging Policy | No user activity retention |
This legal validation has helped strengthen Windscribe’s reputation as a privacy-respecting VPN service.
Windscribe’s Position Among the Top VPN Services in 2026
Within the broader landscape of the top VPN providers in 2026, Windscribe occupies a distinctive niche as the most advanced ad-blocking and browser privacy VPN platform. Its combination of powerful filtering tools, customizable network behavior, and generous free tier has made it particularly popular among users who prioritize control and flexibility.
While it may not offer the largest server network or the most extensive third-party audit history, Windscribe’s robust feature set, strong performance, and transparent privacy practices continue to make it one of the most appealing VPN options for users seeking customizable online privacy solutions.
Overview of the Global VPN Market and Macroeconomic Environment
The global virtual private network industry has evolved into a sophisticated and highly segmented market by 2026. Rather than functioning as a single unified sector, the VPN ecosystem now consists of multiple interconnected segments that serve different technological and economic purposes. The two dominant segments are the commercial enterprise VPN market and the consumer privacy VPN market. Each segment operates under different adoption drivers, infrastructure requirements, and revenue models.
The enterprise segment remains the dominant contributor to total VPN revenue. Organizations worldwide continue to deploy VPN technologies as part of broader cybersecurity architectures, particularly as companies transition toward Zero Trust Network Access frameworks. These architectures require continuous authentication and encrypted communication channels for employees, contractors, and distributed systems. As a result, enterprise VPN solutions remain deeply embedded within modern digital infrastructure.
Within the commercial VPN ecosystem, remote access VPN solutions account for the overwhelming majority of deployments. The persistence of remote and hybrid work environments has permanently reshaped enterprise networking strategies. Employees now frequently access internal corporate systems from geographically dispersed locations, making encrypted remote connectivity essential for maintaining both operational continuity and cybersecurity compliance.
Commercial Versus Consumer VPN Market Structure
The VPN market can be broadly divided into two structural segments that define how products are developed and sold.
| Market Segment | Primary Users | Core Use Cases | Revenue Contribution |
|---|---|---|---|
| Commercial VPN | Enterprises, corporate IT departments | Secure remote access, internal network protection, ZTNA integration | Majority of total market revenue |
| Consumer VPN | Individual users and households | Privacy protection, streaming access, bypassing censorship | Smaller but rapidly growing segment |
The commercial segment currently controls more than seventy-seven percent of the total global VPN market revenue. This dominance reflects the widespread adoption of enterprise cybersecurity solutions that rely heavily on encrypted network tunnels and secure identity verification systems.
Remote access VPN technology represents the backbone of this enterprise infrastructure. By 2026, approximately eighty-six percent of the commercial VPN market is composed of remote access solutions designed to support remote employees, contractors, and distributed workforces.
Geographic Distribution of VPN Market Revenue
Although VPN adoption is expanding worldwide, revenue distribution remains uneven across geographic regions. North America continues to generate the largest share of global VPN revenue due to high enterprise cybersecurity spending, advanced cloud infrastructure adoption, and strong regulatory compliance requirements.
In 2026, North America accounts for slightly more than thirty-seven percent of the total global VPN market. However, the fastest growth rates are emerging in the Asia-Pacific region. Countries throughout Asia are experiencing rapid digital transformation, increased internet penetration, and growing concerns about online censorship and surveillance.
India in particular has experienced one of the most dramatic increases in VPN adoption. Estimates suggest that between forty-three and forty-five percent of Indian internet users now utilize VPN services in some capacity. This surge is driven by several factors including regulatory restrictions, data privacy concerns, and the growing popularity of global streaming platforms.
Global VPN Market Growth Forecast
The overall size of the VPN market has expanded rapidly over the past decade, driven by cybersecurity concerns, remote work expansion, and increasing digital surveillance.
| Market Metric | 2020 (Actual) | 2023 (Actual) | 2025 (Estimated) | 2026 (Forecast) | 2030 (Projected) | 2035 (Projected) |
|---|---|---|---|---|---|---|
| Global Market Value (USD Billion) | $31.3 | $54.0 | $77.8 | $108.57 | $193.5 | $481.5 |
| North American Revenue Share (%) | 35% | 36% | 37% | 37.5% | 38% | 39% |
| Remote Access Segment Share (%) | 80% | 82% | 85% | 86% | 88% | 90% |
| Consumer Adoption (USA, % Population) | 32% | 38% | 42% | 44% | 52% | 65% |
The projected growth trajectory indicates that the global VPN industry could exceed four hundred eighty billion dollars by 2035 if current adoption trends continue. This growth reflects both enterprise cybersecurity investments and expanding consumer demand for privacy-enhancing technologies.
Consumer Adoption and User Demographics
Consumer VPN adoption has also reached historically high levels. By 2026, approximately forty-two percent of Americans report using a VPN service at least occasionally. However, only about forty percent of these users actively connect to their VPN service on a daily basis.
This difference suggests that many users primarily activate VPNs for specific activities such as accessing restricted content, securing public Wi-Fi connections, or protecting sensitive communications rather than maintaining constant encryption.
Consumer VPN Usage Patterns
| User Metric | Observed Value |
|---|---|
| Total U.S. VPN Users | 42% of population |
| Daily VPN Usage | 40% of VPN users |
| Occasional VPN Usage | 60% of VPN users |
These figures demonstrate that VPN technology has moved beyond niche cybersecurity circles and has entered mainstream consumer usage.
Generational Distribution of VPN Users
One of the most notable characteristics of VPN adoption is its strong generational skew. Younger internet users demonstrate significantly higher adoption rates than older demographics. This trend likely reflects higher digital literacy, greater awareness of online privacy concerns, and more frequent engagement with global digital services.
| Age Group | Share of VPN Users |
|---|---|
| Ages 16–24 | 35% |
| Ages 25–34 | 33% |
| Ages 35–54 | 28% |
| Ages 55+ | 4% |
Combined, Generation Z and younger Millennials account for approximately sixty-six percent of all VPN users worldwide. The extremely low adoption rate among users over the age of fifty-five highlights a significant generational divide in digital privacy awareness and cybersecurity practices.
Education and Socioeconomic Factors in VPN Adoption
Education level also plays a significant role in determining VPN usage patterns. Studies indicate that individuals with university-level or postgraduate education are disproportionately represented among VPN users.
This correlation likely stems from several factors including greater awareness of data privacy issues, higher levels of technical literacy, and increased exposure to global digital platforms.
VPN Adoption by Education Level
| Education Level | Relative VPN Adoption |
|---|---|
| Postgraduate Degree | Very High |
| University Degree | High |
| Secondary Education | Moderate |
| Below Secondary Education | Low |
Higher education levels are often associated with occupations that involve remote work, international communication, and digital research activities, all of which increase the likelihood of VPN usage.
Future Outlook for the VPN Industry
The macroeconomic outlook for the VPN industry remains highly positive. Several long-term technological and societal trends continue to fuel demand for encrypted network services.
Key drivers include the global expansion of remote work, rising cybersecurity threats, increasing government surveillance, and growing consumer awareness of online privacy. Additionally, the continued rollout of high-speed internet infrastructure and mobile connectivity across emerging markets is expected to further accelerate VPN adoption worldwide.
As the digital economy continues to expand, VPN technologies are likely to remain a critical component of both enterprise security architectures and individual privacy protection strategies.
Technical Paradigms in the VPN Industry: Artificial Intelligence, Quantum Readiness, and Protocol Evolution
The technological foundation of the VPN industry in 2026 is undergoing one of the most significant transformations since the introduction of modern encrypted tunneling protocols. Traditional cryptographic systems that have long protected internet communications are gradually being replaced or augmented by quantum-resistant algorithms, artificial intelligence–driven network management systems, and highly adaptive communication protocols.
This shift is largely driven by the rapid progress of quantum computing and the increasing complexity of modern cyber threats. VPN providers are no longer simply encrypting internet traffic; they are building adaptive, autonomous security platforms capable of resisting both present and future computational attacks.
Quantum Computing and the Threat to Classical Encryption
One of the most important drivers of cryptographic evolution is the anticipated emergence of quantum computers capable of breaking widely used public-key cryptographic systems. This event is commonly referred to as “Q-Day,” the point at which a sufficiently powerful quantum computer could execute Shor’s Algorithm to compromise widely deployed encryption schemes such as RSA and Elliptic Curve Cryptography.
Current projections suggest that this milestone could occur sometime around 2030, although the exact timeline remains uncertain. Because encrypted communications intercepted today could potentially be decrypted in the future using quantum computers, cybersecurity professionals have adopted a defensive strategy known as “harvest now, decrypt later.”
Under this threat model, attackers may collect large volumes of encrypted data today and store it until quantum technology becomes capable of breaking the encryption. To counter this risk, VPN providers have begun transitioning to cryptographic algorithms specifically designed to resist quantum computational attacks.
Migration Toward Post-Quantum Cryptography
The global transition to quantum-resistant encryption has been guided primarily by standards developed through the U.S. National Institute of Standards and Technology Post-Quantum Cryptography initiative. After several years of evaluation, NIST finalized several algorithms designed to withstand quantum computational attacks.
Among these, lattice-based cryptography has emerged as the most widely adopted approach for secure key exchange within VPN systems.
The most prominent algorithm in this category is ML-KEM, formerly known as CRYSTALS-Kyber. This algorithm replaces traditional key exchange systems such as Diffie-Hellman and RSA within next-generation VPN implementations.
Although symmetric encryption algorithms like AES-256 remain relatively resilient against quantum attacks, quantum search algorithms such as Grover’s Algorithm reduce the effective security of symmetric encryption by roughly half. This means that AES-256 provides security equivalent to approximately 128-bit strength against a quantum adversary.
For this reason, modern VPN systems combine large symmetric keys with post-quantum key exchange algorithms to maintain strong security guarantees.
Post-Quantum Cryptographic Standards
| NIST PQC Standard | Technical Purpose | Performance Impact | Adoption Status in 2026 |
|---|---|---|---|
| ML-KEM-768 | Key encapsulation mechanism based on lattice cryptography | Minimal increase in connection latency | Fully deployed by several leading VPN providers |
| ML-DSA | Digital signature algorithm for authentication | Large signature sizes and slower handshake processes | Currently in pilot implementations |
| SLH-DSA | Stateless hash-based signature algorithm | High computational overhead | Used in specialized high-security environments |
| NordLynx (PQC variant) | Integration of WireGuard protocol with ML-KEM key exchange | Near-native connection speeds | Fully deployed across major operating systems |
These post-quantum cryptographic systems represent a fundamental change in how secure communications are established and authenticated.
Implementation Challenges in Post-Quantum Encryption
Despite the strong security advantages of post-quantum algorithms, their deployment introduces several engineering challenges. One of the most significant issues involves the size of cryptographic signatures generated by these algorithms.
For example, the digital signatures produced by ML-DSA can exceed the size of an entire traditional HTTPS handshake. Such large signatures increase network overhead and can cause packet fragmentation, which may result in slower connection establishment or even connection timeouts.
To address these challenges, VPN providers have implemented protocol optimizations designed to compress cryptographic messages and improve handshake efficiency.
One major milestone occurred when a leading VPN provider completed full deployment of post-quantum cryptographic support across major operating systems including Linux, Windows, macOS, iOS, and Android. This implementation integrated ML-KEM into a modified version of the WireGuard protocol, allowing the system to maintain near-native connection speeds despite the additional cryptographic complexity.
Artificial Intelligence and Autonomous Network Security
Alongside the evolution of cryptography, artificial intelligence has become a central component of modern VPN infrastructure. By 2026, AI systems are no longer used solely for analytics or marketing; they have become active participants in network defense and traffic management.
This shift has been described as the emergence of “agentic AI,” a class of autonomous systems capable of analyzing network conditions, planning defensive strategies, and executing operational decisions with minimal human supervision.
Within VPN environments, these AI systems perform several critical functions.
AI Applications in VPN Network Operations
| AI Application | Operational Purpose |
|---|---|
| Traffic pattern analysis | Detect abnormal network behavior and potential attacks |
| Dynamic routing optimization | Automatically redirect traffic to reduce congestion |
| Resource allocation | Balance server loads across global infrastructure |
| Threat detection | Identify malicious traffic patterns in real time |
| Infrastructure resilience | Automatically reroute connections during outages |
These capabilities allow VPN networks to operate with greater efficiency and resilience while responding to evolving cybersecurity threats.
AI and Protocol Stealth Technologies
Artificial intelligence has also improved the ability of VPN protocols to evade network censorship systems. Many governments deploy technologies known as Deep Packet Inspection systems to identify and block VPN traffic.
To bypass these restrictions, several VPN providers have developed advanced stealth protocols designed to disguise encrypted traffic as ordinary web communication.
Machine learning models analyze patterns of standard internet traffic and adapt VPN packet structures to mimic these patterns.
AI-Enhanced Stealth Protocols
| Protocol Technology | Purpose | Key Functionality |
|---|---|---|
| NordWhisper | Traffic obfuscation protocol | Mimics HTTPS communication patterns |
| Stealth Protocol (Proton) | DPI bypass system | Masks VPN packets as normal encrypted web traffic |
| AI-based packet shaping | Adaptive traffic patterns | Reduces detection by censorship systems |
These technologies significantly increase the likelihood that VPN connections will remain undetected in restrictive network environments.
Predictive Optimization of Server Infrastructure
Another major role of artificial intelligence in VPN systems is predictive infrastructure management. AI algorithms analyze historical traffic patterns and real-time usage data to anticipate network congestion before it occurs.
By predicting traffic surges, these systems can proactively shift resources across the server network to maintain optimal performance.
Predictive Network Optimization
| Optimization Function | Operational Benefit |
|---|---|
| Traffic forecasting | Anticipates demand spikes across regions |
| Server allocation | Automatically scales server capacity |
| Latency reduction | Routes users to optimal server nodes |
| Network resilience | Improves stability during peak usage |
This predictive capability allows VPN providers to deliver faster and more reliable connections without requiring manual infrastructure adjustments.
The Emerging AI Security Arms Race
While artificial intelligence strengthens network defenses, it also empowers cyber attackers. The same technologies that enable advanced traffic analysis can also be used to generate highly sophisticated cyberattacks.
One emerging threat involves the use of deepfake technology to bypass identity verification systems. AI models can generate synthetic voice recordings or video footage that imitate real individuals, potentially compromising multi-factor authentication mechanisms.
Emerging AI-Driven Security Threats
| Threat Type | Description |
|---|---|
| Deepfake voice cloning | Synthetic audio used to impersonate users during authentication |
| Synthetic video generation | AI-generated video used to bypass facial verification |
| Automated intrusion systems | AI agents designed to probe network vulnerabilities |
| Traffic mimicry attacks | Malware that imitates legitimate traffic patterns |
This dynamic creates an ongoing technological arms race between autonomous defensive systems and increasingly sophisticated automated attackers.
Future Technical Direction of VPN Systems
The convergence of post-quantum cryptography, artificial intelligence, and advanced networking protocols signals a new phase in the evolution of VPN technology. VPN providers are transitioning from simple encryption services into complex, adaptive security platforms capable of responding to both classical and quantum computational threats.
As quantum computing capabilities continue to advance and AI technologies become more sophisticated, the VPN industry will likely remain at the forefront of cryptographic research and secure communication engineering. These developments will shape not only VPN technologies but also the broader architecture of secure internet communications in the coming decades.
Comparative Technical Performance and Service Reliability in the VPN Industry
The evaluation of VPN services in 2026 increasingly relies on measurable technical performance indicators rather than marketing claims. Independent benchmarking laboratories and large-scale testing environments now conduct standardized evaluations that analyze download speeds, upload throughput, latency impact, streaming success rates, and encryption reliability.
The following comparative analysis synthesizes testing results from March 2026, providing a structured overview of how leading VPN services perform under controlled conditions. These tests were conducted on a standardized 100 Mbps internet connection to ensure consistent comparison across providers.
Global Speed and Latency Benchmarks
Speed performance remains one of the most critical metrics when evaluating VPN services. Encryption processes and routing overhead can introduce network delays, making it essential for providers to maintain high bandwidth retention and low latency.
The following results represent local performance benchmarks using nearby servers to minimize geographic distance effects.
Global VPN Speed and Latency Performance (March 2026)
| Rank | VPN Service | Download Speed | Upload Speed | Latency (Ping) |
|---|---|---|---|---|
| 1 | NordVPN | 98.5 Mbps | 94 Mbps | 1 ms |
| 2 | ExpressVPN | 98 Mbps | 92 Mbps | 2 ms |
| 3 | Proton VPN | 98 Mbps | 92 Mbps | 2 ms |
| 4 | Hide.me | 98 Mbps | 92 Mbps | 2 ms |
| 5 | Surfshark | 97.5 Mbps | 93 Mbps | 2 ms |
| 6 | Private Internet Access (PIA) | 97 Mbps | 91 Mbps | 2 ms |
| 7 | IPVanish | 96 Mbps | 90 Mbps | 3 ms |
| 8 | Windscribe | 96 Mbps | 91 Mbps | 3 ms |
| 9 | CyberGhost | 94 Mbps | 88 Mbps | 4 ms |
| 10 | PrivateVPN | 93 Mbps | 85 Mbps | 5 ms |
The results demonstrate that modern VPN protocols such as WireGuard and optimized proprietary protocols have significantly reduced the traditional speed penalties associated with encrypted tunneling. Most leading providers now maintain download speeds above 90 percent of the baseline connection rate.
NordVPN leads the benchmark with a measured download speed of 98.5 Mbps and extremely low latency of only one millisecond. Several other services, including ExpressVPN and Proton VPN, achieve nearly identical performance levels.
Latency performance is particularly important for real-time applications such as gaming, voice communication, and financial trading platforms. Even minor increases in ping times can significantly affect user experience in these scenarios.
Speed Retention and Real-World Reliability
While laboratory speed tests provide useful baseline comparisons, real-world reliability is determined by sustained performance across global server networks. Continuous monitoring over extended testing periods provides deeper insight into how VPN services perform under everyday usage conditions.
The following dataset represents aggregated results from thirty days of continuous testing across multiple geographic nodes.
VPN Speed Retention and Streaming Reliability
| VPN Provider | Average Speed Retention | Streaming Hit Rate | Verified No-Logs Audit |
|---|---|---|---|
| IPVanish | 90.1% | 75.0% | Leviathan Security / Schellman |
| Proton VPN | 88.6% | 100.0% | Securitum |
| Surfshark | 88.3% | 100.0% | Deloitte |
| NordVPN | 87.8% | 100.0% | Deloitte |
| Private Internet Access (PIA) | 86.8% | 66.7% | Deloitte |
| ExpressVPN | 86.5% | 87.5% | KPMG |
| PureVPN | 85.8% | 100.0% | KPMG (Continuous Audit) |
Speed retention represents the percentage of baseline bandwidth maintained after VPN encryption and routing overhead. Higher retention scores indicate more efficient network optimization and lower performance degradation.
Among the tested providers, IPVanish achieved the highest average speed retention at 90.1 percent. This performance advantage is often attributed to the company’s direct control over its server infrastructure and optimized routing systems.
Streaming Compatibility and Content Access
Another major metric in VPN performance evaluation is streaming compatibility. Many streaming services attempt to block VPN traffic using IP reputation databases and behavioral analysis systems.
The streaming hit rate measures the percentage of successful attempts to access region-restricted streaming platforms over a prolonged testing period.
Streaming Compatibility Comparison
| VPN Provider | Streaming Success Rate |
|---|---|
| Proton VPN | 100% |
| Surfshark | 100% |
| NordVPN | 100% |
| PureVPN | 100% |
| ExpressVPN | 87.5% |
| IPVanish | 75% |
| Private Internet Access (PIA) | 66.7% |
Several VPN providers demonstrate extremely high streaming compatibility, achieving success rates of 100 percent during testing. These services typically employ specialized server infrastructure and rotating IP address pools to bypass streaming platform detection systems.
By contrast, services such as Private Internet Access focus more heavily on privacy and customization rather than streaming optimization, which can reduce their success rates in bypassing regional restrictions.
Privacy Audits and Security Verification
Technical performance alone does not fully determine the reliability of a VPN service. Independent security audits play an increasingly important role in verifying whether providers adhere to their privacy claims, particularly regarding no-logs policies.
Third-party cybersecurity firms conduct infrastructure inspections, software audits, and logging verification procedures to ensure that user activity data is not being recorded.
Independent Privacy Audit Comparison
| VPN Provider | Audit Organization | Audit Scope |
|---|---|---|
| NordVPN | Deloitte | Infrastructure and no-logs verification |
| Surfshark | Deloitte | No-logs policy validation |
| Proton VPN | Securitum | Application and infrastructure security |
| ExpressVPN | KPMG | Server infrastructure and privacy policy |
| PureVPN | KPMG | Continuous monitoring audit framework |
| IPVanish | Leviathan Security / Schellman | Logging verification |
| Private Internet Access (PIA) | Deloitte | No-logs policy validation |
These audits provide external validation that VPN providers do not retain user activity logs that could compromise privacy.
Overall Reliability and Service Consistency
When combining speed performance, streaming compatibility, and privacy verification, several VPN providers consistently rank at the top of the industry.
Overall Performance Summary
| Category | Leading Providers |
|---|---|
| Highest Speed Retention | IPVanish |
| Lowest Latency | NordVPN |
| Best Streaming Compatibility | Proton VPN, Surfshark, NordVPN, PureVPN |
| Most Extensive Audit Verification | ExpressVPN |
| Best Balance of Speed and Streaming | NordVPN |
This comparative analysis demonstrates that the modern VPN industry has achieved significant technological maturity. The majority of leading providers now deliver near-native internet speeds while maintaining strong encryption and privacy protections.
As network protocols continue to evolve and infrastructure becomes increasingly optimized, future VPN services will likely focus on integrating advanced cryptographic protections, artificial intelligence-driven traffic management, and enhanced resilience against emerging cyber threats.
Strategic Value of Dedicated IP Addresses in the VPN Ecosystem
By 2026, dedicated IP addresses have become an increasingly important feature within the VPN market, particularly for users requiring stable and reputation-sensitive internet connectivity. Unlike traditional VPN connections that assign users a shared IP address used simultaneously by multiple subscribers, a dedicated IP address is reserved exclusively for a single customer.
This exclusivity provides several technical advantages, particularly for enterprise users, remote professionals, and individuals who rely on consistent network identity for authentication systems or automated online services. As digital security systems become more sensitive to unusual network behavior, the demand for dedicated IP addresses has grown steadily.
Understanding Dedicated IP Architecture
In standard VPN configurations, hundreds or even thousands of users may share a single public IP address. While this approach improves anonymity by blending user traffic together, it can also lead to several operational limitations.
For example, shared IP addresses are frequently flagged by websites and automated security systems when suspicious behavior is detected from any one user within the shared pool. This can trigger CAPTCHAs, authentication challenges, or even temporary blocks.
Dedicated IP infrastructure solves this issue by assigning a unique IP address to a single subscriber.
Shared vs Dedicated IP Characteristics
| Feature Category | Shared VPN IP Address | Dedicated VPN IP Address |
|---|---|---|
| Number of Users per IP | Multiple users | Single user only |
| CAPTCHA Frequency | Higher likelihood | Significantly reduced |
| IP Reputation Stability | Variable due to shared traffic | Stable and consistent |
| Anonymity Level | Higher due to mixed user traffic | Lower but still encrypted |
| Suitable Use Cases | General browsing and privacy | Professional or business operations |
While shared IP systems maximize anonymity, dedicated IP addresses provide predictability and operational stability.
Primary Use Cases for Dedicated IP Addresses
The growth of remote work and cloud-based services has created several scenarios in which dedicated IP addresses offer clear advantages.
Organizations frequently rely on IP-based authentication systems that grant access to internal resources only when a user connects from an approved IP address. Dedicated IP addresses simplify this process by providing a consistent connection endpoint.
Common Dedicated IP Use Cases
| Use Case | Operational Benefit |
|---|---|
| Corporate remote access | Enables secure access to internal company networks |
| Database administration | Allows secure connections to restricted servers |
| Email marketing infrastructure | Maintains stable IP reputation to prevent spam filtering |
| Secure file transfer systems | Ensures consistent authentication credentials |
| Reduced CAPTCHA interruptions | Avoids IP reputation issues caused by shared usage |
These advantages have made dedicated IP services particularly popular among remote professionals and digital businesses.
Privacy-Preserving Dedicated IP Allocation Systems
Although dedicated IP addresses introduce stability benefits, they also present potential privacy risks. If the VPN provider maintains direct records linking a customer account to a specific IP address, this information could theoretically compromise anonymity.
To address this concern, several leading VPN providers have implemented privacy-preserving allocation systems based on tokenized authentication mechanisms.
Tokenized Dedicated IP Allocation Model
| System Component | Functional Role |
|---|---|
| Payment verification system | Confirms that a customer has purchased the dedicated IP add-on |
| Token generation system | Issues a cryptographic token representing the purchase |
| Provisioning server | Assigns the dedicated IP address based on token validation |
| Account database | Stores billing data but does not store IP assignment mapping |
Under this architecture, the billing system confirms that the user has paid for the service, while the infrastructure provisioning system assigns the IP address using anonymous tokens. As a result, the provider cannot directly link the specific IP address to the user’s account identity.
This privacy-preserving design has become increasingly common among leading VPN services.
Dedicated IP Availability and Pricing Comparison
Several major VPN providers offer dedicated IP services as optional add-ons to their standard VPN subscriptions. Pricing typically depends on the number of available locations and the provider’s underlying infrastructure costs.
The following table compares the pricing structures of several prominent VPN providers offering dedicated IP addresses.
Dedicated IP Pricing Comparison
| Provider | Dedicated IP Monthly Fee | Number of Available Countries | Effective Monthly Total |
|---|---|---|---|
| Private Internet Access (PIA) | $2.50 | 5 | $3.69 |
| NordVPN | $3.69 | 28 | $4.49 |
| Surfshark | $3.75 | 20 | $4.48 |
| ExpressVPN | $3.99 | 5 | $9.42 |
| PureVPN | $4.45 | 10 | $6.24 |
| CyberGhost | Private pricing | 12 | Not publicly listed |
Effective monthly totals represent the combined cost of the base VPN subscription and the dedicated IP add-on when purchased under the longest available subscription plans.
NordVPN currently offers the widest geographic selection of dedicated IP locations, covering approximately twenty-eight countries. This wide distribution allows users to maintain stable identities in multiple regions.
Performance Implications of Dedicated IP Usage
Dedicated IP addresses can also improve network performance in certain scenarios. Because traffic is not shared among multiple users, there is reduced risk of congestion or throttling triggered by abusive activity from other subscribers.
Dedicated IP Performance Advantages
| Performance Factor | Impact |
|---|---|
| IP reputation stability | Reduces service blocks and verification challenges |
| Connection reliability | Maintains consistent access credentials |
| Network throughput | Avoids bandwidth contention from shared users |
| Authentication reliability | Improves compatibility with IP-based security systems |
These benefits are particularly valuable for users running automated systems, web services, or long-duration network sessions.
Balancing Privacy and Stability
Despite their advantages, dedicated IP addresses represent a trade-off between anonymity and operational stability. Shared IP systems provide greater anonymity by mixing traffic from multiple users, making it difficult to identify individual connections.
Dedicated IP addresses, by contrast, provide consistent identity characteristics that can be recognized by external systems.
Dedicated IP Trade-Off Analysis
| Factor | Dedicated IP | Shared IP |
|---|---|---|
| Connection stability | Very high | Moderate |
| Online anonymity | Moderate | Very high |
| CAPTCHA frequency | Low | Higher |
| Corporate compatibility | Excellent | Limited |
For privacy-focused users seeking maximum anonymity, shared IP configurations remain preferable. However, for users requiring reliability and consistent network identity, dedicated IP addresses provide significant operational benefits.
Future Role of Dedicated IP Infrastructure
As digital security systems continue to evolve, the strategic importance of dedicated IP infrastructure is likely to increase. Enterprise authentication systems, financial platforms, and cloud environments increasingly rely on stable network identity verification to prevent unauthorized access.
At the same time, improvements in tokenized IP allocation models ensure that dedicated IP services can maintain strong privacy protections without exposing user identities.
This balance between operational stability and privacy protection ensures that dedicated IP addresses will remain a key component of the VPN ecosystem as it continues to evolve throughout the remainder of the decade.
Regulatory Landscape and Jurisdictional Integrity in the VPN Industry
In the global VPN industry, jurisdiction plays a critical role in determining the credibility, legal resilience, and privacy reliability of a service provider. The legal environment governing a VPN company influences how user data is handled, what obligations exist for data retention, and whether authorities can compel companies to disclose information about their customers.
By 2026, the regulatory landscape surrounding cybersecurity and encrypted communication services has become significantly more structured. Governments and supranational institutions have introduced stricter compliance frameworks designed to improve software security while also increasing oversight of digital service providers.
One of the most influential regulatory developments shaping the VPN ecosystem is the Cyber Resilience Act. This legislation introduces comprehensive security obligations for companies distributing digital products and software within the European market.
Impact of the Cyber Resilience Act on VPN Providers
The Cyber Resilience Act establishes mandatory cybersecurity requirements for software suppliers operating within the European Union. Under this framework, companies must adopt secure software development practices, implement continuous vulnerability monitoring systems, and maintain rapid incident response procedures.
For VPN providers, this means that practices previously considered optional industry best practices have now become legal compliance requirements.
Cyber Resilience Act Compliance Requirements
| Regulatory Requirement | Operational Impact on VPN Providers |
|---|---|
| Secure Development Lifecycle (SDL) | Mandatory integration of secure coding and testing practices |
| Vulnerability Management | Continuous monitoring and patching of security flaws |
| Incident Reporting | Mandatory disclosure of major security breaches |
| Product Lifecycle Security | Ongoing security maintenance for distributed software |
| Supply Chain Security | Verification of third-party software dependencies |
These requirements aim to improve the overall resilience of digital infrastructure while reducing the likelihood of large-scale cyber incidents.
The Role of Jurisdiction in VPN Trustworthiness
Beyond regulatory compliance, jurisdiction remains one of the most important criteria when evaluating VPN providers. The country in which a company is legally registered determines which laws govern its operations, including whether authorities can compel companies to retain or disclose user data.
VPN providers are often categorized based on their relationship to international intelligence-sharing alliances, commonly referred to as the Five Eyes, Nine Eyes, and Fourteen Eyes networks.
These alliances represent cooperative intelligence agreements between governments that share surveillance data and investigative resources.
Intelligence Alliance Classification
| Alliance Group | Member Countries | Surveillance Cooperation Level |
|---|---|---|
| Five Eyes | United States, United Kingdom, Canada, Australia, New Zealand | Highest intelligence integration |
| Nine Eyes | Five Eyes + Netherlands, Denmark, France, Norway | Expanded surveillance collaboration |
| Fourteen Eyes | Nine Eyes + Germany, Belgium, Italy, Spain, Sweden | Extended intelligence sharing |
VPN providers headquartered outside these alliances are generally considered to operate under more privacy-friendly legal environments.
Jurisdictional Analysis of Major VPN Providers
Several leading VPN providers operate in jurisdictions specifically chosen for their favorable privacy laws and resistance to international surveillance requests.
The following overview summarizes the legal environments associated with major VPN providers in 2026.
VPN Provider Jurisdiction Comparison
| Jurisdiction | Example Providers | Legal Characteristics |
|---|---|---|
| Panama | NordVPN | No mandatory data retention laws; historically resistant to foreign legal demands |
| British Virgin Islands | ExpressVPN, PureVPN | Independent legal system separate from the United Kingdom; no data retention laws |
| Switzerland | Proton VPN | Outside EU and EEA; strong privacy protections under Swiss Federal Data Protection law |
| Romania | CyberGhost, Bitdefender | EU member state, but courts have ruled mandatory data retention unconstitutional |
| Netherlands | Surfshark | Member of Nine Eyes intelligence alliance; privacy protections validated through audits |
| United States | Private Internet Access, IPVanish | Member of Five Eyes alliance; stronger surveillance powers but some providers proven no-logs in court |
Each jurisdiction presents a different balance between regulatory oversight and user privacy protection.
Privacy Advantages of Panama
Panama remains one of the most favorable jurisdictions for privacy-focused technology companies. The country has no mandatory data retention laws requiring internet service providers or technology companies to store user activity records.
This legal environment has allowed several VPN providers to operate strict no-logs policies without facing conflicting regulatory requirements.
Panama Jurisdiction Benefits
| Legal Factor | Privacy Impact |
|---|---|
| No mandatory data retention | Providers not required to store user activity |
| Limited international warrant recognition | Foreign legal requests often rejected |
| Independent judiciary | Reduced influence from foreign governments |
These characteristics make Panama one of the most commonly cited jurisdictions for privacy-centric VPN providers.
Legal Framework of the British Virgin Islands
The British Virgin Islands operate under a unique legal structure as a British Overseas Territory with its own judicial system. Despite the connection to the United Kingdom, the territory maintains legal autonomy in many areas of digital regulation.
British Virgin Islands Privacy Characteristics
| Legal Factor | Privacy Impact |
|---|---|
| Separate legal system | Independent court authority |
| No data retention laws | Providers not obligated to store connection logs |
| Limited external jurisdiction | Foreign legal requests require local court approval |
These conditions have made the jurisdiction particularly attractive for companies seeking operational independence from surveillance alliances.
Switzerland’s Data Protection Framework
Switzerland has long been recognized as one of the strongest privacy jurisdictions in the world. The Swiss Federal Act on Data Protection establishes strict requirements governing how personal information may be collected, stored, and processed.
Switzerland Privacy Framework
| Legal Feature | Protection Provided |
|---|---|
| Federal Data Protection Act | Strict limits on personal data processing |
| Independent judiciary | Strong legal oversight of surveillance requests |
| Non-membership in EU or intelligence alliances | Reduced international data sharing obligations |
These legal protections contribute to Switzerland’s reputation as a safe jurisdiction for privacy-focused services.
The Netherlands and Intelligence Cooperation
The Netherlands is a member of the Nine Eyes intelligence-sharing alliance, meaning its government participates in international surveillance cooperation programs. However, VPN providers operating within the country have still managed to demonstrate compliance with strong privacy standards through independent security audits.
Dutch Regulatory Characteristics
| Legal Factor | Implication |
|---|---|
| Nine Eyes membership | Participation in intelligence cooperation |
| EU data protection regulations | Compliance with GDPR privacy rules |
| Independent audits | Verification of no-logs policies |
Although the jurisdiction presents additional surveillance risks compared with some alternatives, independent audits can mitigate many concerns.
United States Jurisdiction and Legal Pressure
The United States presents one of the most complex environments for VPN providers. As a member of the Five Eyes intelligence alliance, the country has extensive surveillance capabilities and legal mechanisms for obtaining information from technology companies.
However, several VPN providers operating within the United States have successfully demonstrated that their no-logs policies are technically enforced.
U.S. Jurisdiction Overview
| Legal Factor | Implication |
|---|---|
| Five Eyes membership | Participation in global intelligence sharing |
| Legal warrants and subpoenas | Authorities can demand company records |
| Court-tested no-logs policies | Some providers proven incapable of providing user data |
These cases demonstrate that strong technical architecture can protect user privacy even in more demanding regulatory environments.
Balancing Compliance and Privacy
The regulatory landscape in 2026 illustrates the growing complexity of operating privacy-focused technologies within an increasingly regulated digital ecosystem. VPN providers must balance legal compliance with cybersecurity regulations while simultaneously protecting the privacy expectations of their users.
Key Factors Influencing VPN Jurisdiction Selection
| Decision Factor | Importance |
|---|---|
| Data retention laws | Determines whether providers must store user activity |
| Intelligence alliance membership | Influences government surveillance powers |
| Judicial independence | Determines resistance to foreign legal requests |
| Cybersecurity regulation | Establishes compliance obligations for software providers |
As cybersecurity regulations continue to evolve and governments expand digital oversight, the choice of jurisdiction will remain one of the most important factors shaping the credibility and trustworthiness of VPN providers worldwide.
User Experience and Mobile Integration in the Modern VPN Ecosystem
By 2026, mobile devices have become the primary platform for VPN usage worldwide. Industry data indicates that more than sixty-seven percent of VPN connections now originate from smartphones and tablets rather than traditional desktop environments. This shift reflects broader global trends in mobile-first internet access, cloud-based productivity tools, and the widespread use of public wireless networks.
As a result, VPN providers have significantly redesigned their products to prioritize mobile application performance, energy efficiency, and seamless integration with mobile operating systems such as iOS and Android. Modern VPN apps are no longer simple connection tools; they now function as comprehensive privacy management platforms that integrate deeply with mobile device ecosystems.
Growth of Mobile VPN Adoption
The rapid increase in mobile VPN usage has been driven by several structural changes in digital behavior. Many users now rely on smartphones as their primary computing device for banking, communication, media consumption, and remote work activities.
Mobile VPN adoption drivers include:
• Increased use of public Wi-Fi networks in cafes, airports, and hotels
• Growing awareness of mobile data privacy risks
• Expansion of mobile streaming platforms
• Rise of remote work and mobile productivity tools
• Greater reliance on smartphones for financial transactions
These factors have encouraged VPN providers to invest heavily in optimizing mobile user experiences.
Mobile VPN Usage Trends
| Category | Observed Trend |
|---|---|
| Share of VPN traffic from mobile devices | 67% |
| Dominant mobile platforms | iOS and Android |
| Primary mobile use cases | Privacy protection, streaming access, public Wi-Fi security |
| Key mobile priorities | Low latency, battery efficiency, automatic connection |
Mobile VPN applications must now balance strong encryption with minimal battery consumption, fast connection establishment, and intuitive user interfaces.
Mobile Application Ratings and Market Perception
User satisfaction ratings across major mobile app stores provide a valuable indicator of how well VPN providers have adapted to the mobile-first internet environment. Ratings from the Apple App Store and Google Play Store reflect real-world user experiences across millions of installations.
Mobile VPN App Ratings in 2026
| VPN Service | App Store Rating (iOS) | Google Play Rating (Android) | Key Mobile Feature |
|---|---|---|---|
| NordVPN | 4.8 / 5.0 | 4.7 / 5.0 | Meshnet file-sharing network |
| IPVanish | 4.5 / 5.0 | 4.4 / 5.0 | Broad platform compatibility |
| Norton VPN | 4.7 / 5.0 | 4.7 / 5.0 | Integrated antivirus ecosystem |
| Surfshark | 4.8 / 5.0 | 4.6 / 5.0 | CleanWeb ad and tracker blocker |
| ExpressVPN | 4.6 / 5.0 | 4.5 / 5.0 | Aircove router integration |
The consistently high ratings across these services demonstrate the maturity of modern VPN mobile applications. Early VPN apps were often criticized for unstable connections, high battery consumption, and limited functionality. However, improvements in mobile operating system integration and network protocol efficiency have significantly improved user experiences.
Integration with Mobile Operating Systems
Modern VPN applications integrate deeply with mobile operating systems, allowing them to automatically activate when certain conditions are detected. This automation improves security while minimizing the need for manual user intervention.
Mobile Operating System Integration Features
| Feature | Functional Purpose |
|---|---|
| Automatic Wi-Fi protection | Automatically activates VPN when connecting to public networks |
| On-demand VPN connections | Enables VPN routing for specific apps |
| Battery optimization modes | Reduces energy consumption during idle periods |
| Secure DNS routing | Protects browsing queries from interception |
| Always-on VPN settings | Maintains continuous encrypted connection |
These features are especially valuable for users who frequently move between trusted and untrusted networks.
Advanced Mobile Privacy Features
VPN providers have also introduced several innovative mobile-specific tools designed to improve digital privacy and identity protection.
Two notable examples include Alternative ID and Meshnet.
Alternative ID Technology
Alternative ID systems allow users to generate temporary online identities when signing up for websites or services. These identities typically include disposable email addresses and randomized personal details.
Alternative ID Functionality
| Feature | Benefit |
|---|---|
| Temporary identity creation | Protects real personal information |
| Disposable email addresses | Reduces spam and data harvesting |
| Identity compartmentalization | Limits tracking across services |
This feature has become particularly popular among privacy-focused users who wish to minimize their digital footprint.
Meshnet and Peer-to-Peer Network Routing
One of the most innovative mobile features introduced in recent years is Meshnet technology. This system allows users to create encrypted peer-to-peer networks between trusted devices.
Under this model, one device can route its internet traffic through another authorized device located elsewhere in the world.
Meshnet Network Capabilities
| Function | Description |
|---|---|
| Secure file transfer | Enables encrypted file sharing between connected devices |
| Remote device access | Allows secure access to personal devices from anywhere |
| Peer-to-peer VPN routing | Routes traffic through trusted devices |
| Local network simulation | Allows devices to appear as if on the same network |
This functionality can be particularly useful for bypassing certain streaming platform restrictions. Some streaming services restrict access when they detect that a user is connecting from a different geographic location than the account owner. By routing traffic through a trusted device located at the owner’s primary residence, Meshnet allows the user to appear as if they are accessing the service from that location.
Mobile Security Challenges
Despite the significant advancements in mobile VPN technology, several security challenges remain. Mobile devices are inherently more vulnerable to certain types of attacks due to their constant connectivity and frequent use of public networks.
Common Mobile VPN Threats
| Threat Type | Description |
|---|---|
| Rogue Wi-Fi hotspots | Fake networks designed to intercept user traffic |
| Mobile malware | Malicious apps that monitor network activity |
| Data leakage through background apps | Applications transmitting data outside VPN tunnels |
| Device fingerprinting | Tracking based on hardware and software characteristics |
VPN providers continue to develop improved mobile security mechanisms to mitigate these risks.
Future Evolution of Mobile VPN Experiences
Looking ahead, mobile integration will likely become an even more central component of VPN service design. As mobile devices continue to replace traditional computing platforms for many users, VPN applications will evolve to provide broader privacy management capabilities.
Future developments may include AI-powered connection optimization, deeper integration with mobile operating system security frameworks, and enhanced decentralized networking features.
The shift toward mobile-first connectivity has permanently reshaped how VPN services are designed, deployed, and evaluated. Providers that successfully combine strong encryption, efficient mobile performance, and intuitive user experiences will remain at the forefront of the rapidly expanding VPN market.
Strategic Outlook of the Global VPN Industry
The virtual private network industry in 2026 has entered a transformative phase often described as the era of existential cryptography. In this stage of technological evolution, the long-term viability of VPN providers increasingly depends on their readiness for the emerging post-quantum computing environment. As quantum research advances and the possibility of large-scale quantum decryption becomes more realistic, VPN services must redesign their security architectures to ensure long-term cryptographic resilience.
Traditional encryption systems that once formed the backbone of secure internet communication are gradually being replaced by post-quantum cryptographic frameworks. Providers that fail to integrate quantum-resistant encryption algorithms risk exposing their users to future threats where encrypted data intercepted today could potentially be decrypted by quantum systems in the coming decades.
The analysis of the leading VPN services indicates that several providers have already begun this transition. Services such as NordVPN, Surfshark, and Proton VPN have incorporated post-quantum cryptographic algorithms alongside modern tunneling protocols. In addition to cryptographic upgrades, these providers have deployed artificial intelligence–driven network defense systems designed to monitor traffic patterns, detect anomalies, and dynamically optimize server infrastructure.
Equally important is the verification of privacy claims through independent security audits. Providers that undergo regular inspections by major global auditing firms have established stronger credibility in the cybersecurity community. Continuous verification processes help ensure that privacy policies, such as strict no-logs commitments, are enforced through technical architecture rather than relying solely on corporate statements.
Market Growth and Economic Forecast
The economic trajectory of the VPN market remains exceptionally strong. Over the past decade, the industry has experienced consistent growth driven by increasing cybersecurity threats, remote work expansion, and rising awareness of digital privacy risks.
Forecast models suggest that the global VPN market could expand dramatically between 2020 and 2035.
VPN Market Expansion Forecast
| Year | Estimated Market Value (USD Billion) |
|---|---|
| 2020 | 31.3 |
| 2023 | 54.0 |
| 2025 | 77.8 |
| 2026 | 108.57 |
| 2030 | 193.5 |
| 2035 | 481.5 |
This projected growth represents roughly a fifteen-fold increase in industry size over a fifteen-year period. The expansion is fueled by both enterprise cybersecurity investments and the continued adoption of privacy tools by individual consumers.
Enterprise Influence and Zero Trust Security
A major structural change influencing the VPN industry is the widespread adoption of Zero Trust security frameworks within corporate environments. Zero Trust models assume that no user or device should be automatically trusted simply because it resides inside a corporate network perimeter.
Instead, every access request must be authenticated, verified, and continuously monitored.
Impact of Zero Trust Architecture on VPN Services
| Security Model | Traditional VPN Model | Zero Trust Architecture |
|---|---|---|
| Trust assumption | Internal network users trusted by default | No implicit trust granted |
| Authentication | Single login verification | Continuous authentication |
| Network segmentation | Broad access permissions | Strict micro-segmentation |
| Access control | Location-based trust | Identity-based trust |
As companies transition toward these security architectures, enterprise VPN solutions are evolving into integrated identity verification platforms rather than simple encrypted tunnels.
Evolution of the Consumer VPN Market
While enterprise demand continues to grow, the consumer VPN segment is also undergoing a significant transformation. Early consumer VPN services primarily focused on encrypting internet traffic and allowing users to bypass geographic restrictions.
By 2026, however, many providers have expanded their offerings into comprehensive digital identity protection ecosystems.
Emerging Consumer VPN Service Features
| Feature Category | Purpose |
|---|---|
| Identity monitoring | Detect data breaches involving personal information |
| Alternative digital identities | Protect real personal data during online registrations |
| Integrated antivirus tools | Provide device-level malware protection |
| Secure password management | Protect user credentials across services |
| Encrypted cloud storage | Secure sensitive files and backups |
This broader approach reflects a shift from simple connectivity tools toward complete digital privacy suites.
The Importance of Technical Transparency
In an increasingly complex digital environment, trust has become one of the most valuable assets for VPN providers. Users must rely on the provider’s infrastructure to protect their sensitive communications, making transparency and verifiable security practices essential.
Several providers have distinguished themselves through commitments to open-source development and publicly verifiable privacy policies.
Transparency Leadership Among VPN Providers
| Provider | Transparency Approach |
|---|---|
| Proton VPN | Fully open-source applications and infrastructure transparency |
| Mullvad VPN | Anonymous account system and minimal data collection |
| Private Internet Access | Open-source clients and court-tested no-logs policy |
| NordVPN | Multiple independent security audits |
| Surfshark | Regular privacy audits and infrastructure verification |
Open-source development allows independent security researchers to inspect the code used by VPN applications, ensuring that no hidden tracking mechanisms or vulnerabilities exist within the software.
Legal validation also strengthens trust. In several notable court cases, VPN providers such as Mullvad and Private Internet Access were unable to supply user activity records because their infrastructure was designed not to store such information.
Digital Sovereignty in a Monitored Internet
As digital infrastructure becomes increasingly centralized and algorithmically managed, VPN services play a critical role in enabling individuals to maintain control over their online activities. Governments, corporations, and data brokers now collect unprecedented volumes of information about internet users.
VPN technologies provide one of the most accessible tools for individuals seeking to regain a measure of digital sovereignty.
Digital Sovereignty Benefits of VPN Technology
| Capability | Impact |
|---|---|
| Traffic encryption | Protects communications from interception |
| IP address masking | Reduces tracking by websites and advertisers |
| Secure public Wi-Fi usage | Prevents network-based attacks |
| Censorship circumvention | Enables access to unrestricted information |
While VPN technology cannot solve every privacy challenge, it remains one of the most practical and widely adopted tools for protecting personal data online.
Future Outlook for the VPN Industry
Looking ahead, the long-term success of VPN providers will depend on several key factors.
Key Strategic Priorities for VPN Providers
| Strategic Priority | Importance |
|---|---|
| Post-quantum cryptographic readiness | Protects against future quantum attacks |
| AI-driven network defense | Enables adaptive cybersecurity infrastructure |
| Independent security audits | Strengthens user trust and credibility |
| Transparent development practices | Improves verifiability of privacy claims |
| Integrated identity protection tools | Expands consumer value beyond encryption |
The VPN market has evolved far beyond its early role as a simple privacy tool. It now represents a critical component of modern cybersecurity infrastructure for both individuals and organizations.
As the global internet continues to evolve under increasing surveillance and algorithmic control, VPN technologies will remain an essential mechanism through which users maintain control over their digital identities and communications. Providers that combine technical innovation with transparency and verifiable security practices are likely to dominate the industry in the years ahead.
Conclusion
The global VPN industry in 2026 stands at a defining technological and economic crossroads. What was once considered a niche cybersecurity tool for privacy enthusiasts has evolved into a critical layer of the modern internet infrastructure. As digital surveillance expands, remote work becomes a permanent feature of the global economy, and cyber threats grow more sophisticated, virtual private networks have transitioned from optional utilities into essential tools for both individuals and organizations.
The evaluation of the top 10 VPNs in the world in 2026 demonstrates that the industry has matured significantly in terms of performance, security architecture, transparency, and innovation. Providers such as NordVPN, Surfshark, Proton VPN, ExpressVPN, Private Internet Access, CyberGhost, IPVanish, Mullvad VPN, PureVPN, and Windscribe have each carved out distinct positions within the market by addressing different technical priorities and user requirements.
From ultra-fast connection speeds and streaming compatibility to open-source transparency and post-quantum cryptographic readiness, the modern VPN landscape is defined by diversity in technological approach and specialization in user experience.
The Evolution of VPN Technology
The VPN services leading the market in 2026 are no longer limited to encrypting internet traffic. Instead, they operate as sophisticated digital privacy platforms that integrate advanced cryptographic protocols, AI-driven network optimization, and multi-layer cybersecurity protection.
The integration of modern tunneling technologies such as WireGuard-based protocols has significantly reduced the performance overhead historically associated with VPN encryption. Many top providers now achieve connection speeds exceeding ninety percent of the user’s baseline internet bandwidth, making VPN usage virtually indistinguishable from direct internet connections.
Simultaneously, the emergence of post-quantum cryptographic algorithms marks one of the most important shifts in the history of internet security. Leading VPN providers are preparing for the era of quantum computing by integrating lattice-based encryption methods and next-generation key exchange mechanisms. These innovations ensure that encrypted communications remain secure even in a future where quantum computers could break traditional encryption standards.
This technological transformation highlights an important reality: the VPN services that dominate the market today are those that invest heavily in long-term cryptographic resilience and adaptive network security.
Market Leaders and Their Unique Strengths
Each of the top VPN providers examined in this analysis offers specific strengths that make them attractive to different categories of users.
VPN Provider Specialization Overview
| VPN Provider | Core Strength |
|---|---|
| NordVPN | High performance infrastructure and advanced security suite |
| Surfshark | Unlimited device connections and value-focused pricing |
| Proton VPN | Open-source transparency and Swiss privacy protection |
| ExpressVPN | Exceptional usability and polished user interface |
| Private Internet Access | Advanced customization and open-source clients |
| CyberGhost | Streaming optimization and beginner-friendly interface |
| IPVanish | High-speed infrastructure and unlimited connections |
| Mullvad VPN | Maximum anonymity and privacy-first design |
| PureVPN | Modular add-on services and specialized networking features |
| Windscribe | Powerful ad-blocking and flexible customization tools |
Rather than competing solely on speed or price, the most successful VPN providers in 2026 differentiate themselves through technological specialization and unique feature ecosystems.
For example, some services prioritize strict privacy protections through anonymous account systems and open-source software transparency, while others focus on entertainment access, global server coverage, or enterprise-level network performance.
The Role of Transparency and Trust
In an era defined by algorithmic governance, artificial intelligence, and large-scale data collection, trust has become the most valuable currency in the VPN industry. Users rely on VPN providers to safeguard their digital identities, browsing habits, and personal communications.
As a result, the most credible VPN services have embraced transparency as a core operational principle. This transparency takes several forms, including independent security audits, open-source software development, court-verified no-logs policies, and publicly documented infrastructure practices.
Providers that have undergone repeated third-party security audits by major global firms have strengthened their credibility by allowing external verification of their privacy claims. Meanwhile, open-source VPN applications enable cybersecurity researchers to independently examine software code for vulnerabilities or hidden data collection mechanisms.
This shift toward verifiable privacy architecture ensures that trust in VPN providers is based on measurable technical evidence rather than marketing promises.
Mobile Integration and User Experience
Another defining characteristic of the modern VPN market is the dominance of mobile connectivity. With more than two-thirds of VPN usage now occurring on smartphones and tablets, providers have redesigned their applications to prioritize mobile performance, battery efficiency, and seamless operating system integration.
Mobile VPN clients now include features such as automatic Wi-Fi protection, app-based split tunneling, DNS leak protection, and identity protection services. These tools allow users to maintain secure connections across dynamic network environments without sacrificing convenience or performance.
Additionally, innovative technologies such as peer-to-peer networking systems and decentralized device routing have expanded the functionality of VPN services beyond traditional encrypted tunnels.
This evolution demonstrates that user experience is no longer a secondary consideration in VPN design. Instead, it has become a core factor in determining which services achieve long-term market leadership.
The Strategic Importance of Jurisdiction
The credibility of a VPN provider is also deeply influenced by the legal jurisdiction in which it operates. Countries with strong privacy protections and limited data retention laws provide a more favorable environment for maintaining strict no-logs policies.
In contrast, jurisdictions associated with international surveillance alliances may introduce additional legal pressures on technology companies to cooperate with government investigations.
However, recent developments have shown that strong technical architecture can mitigate many jurisdictional concerns. Several VPN providers operating within surveillance-heavy jurisdictions have successfully demonstrated that their infrastructure does not store identifiable user data.
This reinforces the principle that privacy protection ultimately depends more on technical implementation than on legal promises alone.
The Future of the VPN Industry
Looking ahead, the VPN industry is expected to continue expanding at a rapid pace. Forecast models suggest that the global VPN market could grow dramatically over the next decade as cybersecurity threats intensify and digital privacy concerns become more widespread.
Several emerging trends will likely shape the next generation of VPN technologies:
Key Trends Defining the Future of VPNs
| Trend | Industry Impact |
|---|---|
| Post-quantum cryptography | Protects communications from future quantum attacks |
| Artificial intelligence integration | Enables autonomous network optimization and threat detection |
| Identity protection services | Expands VPN functionality beyond encrypted connections |
| Decentralized networking | Introduces peer-to-peer privacy infrastructures |
| Privacy-focused regulation | Establishes stronger compliance frameworks for providers |
These developments suggest that VPN services will increasingly evolve into comprehensive digital security ecosystems rather than standalone connectivity tools.
Digital Sovereignty in the Modern Internet
Ultimately, the significance of VPN technology extends far beyond encryption protocols and network performance metrics. In a world where digital platforms collect vast quantities of personal data and governments deploy increasingly sophisticated surveillance technologies, VPNs provide one of the few accessible mechanisms for individuals to maintain control over their online activities.
For everyday users, VPN services offer protection against tracking, censorship, and data interception. For businesses and organizations, they provide secure communication channels essential for protecting intellectual property and sensitive information.
The top VPN providers in 2026 demonstrate that it is possible to balance performance, privacy, transparency, and usability within a single technological ecosystem.
As the internet continues to evolve under the pressures of globalization, regulation, and artificial intelligence, VPN technologies will remain a cornerstone of digital freedom and cybersecurity.
Choosing the right VPN service ultimately depends on the specific needs of the user, whether those priorities involve maximum anonymity, high-speed streaming access, advanced customization, or enterprise-grade security.
However, one conclusion remains clear: in the digital landscape of 2026 and beyond, virtual private networks are no longer optional tools for a small group of privacy enthusiasts. They have become fundamental components of a secure, resilient, and user-controlled internet.
If you find this article useful, why not share it with your hiring manager and C-level suite friends and also leave a nice comment below?
We, at the 9cv9 Research Team, strive to bring the latest and most meaningful data, guides, and statistics to your doorstep.
To get access to top-quality guides, click over to 9cv9 Blog.
To hire top talents using our modern AI-powered recruitment agency, find out more at 9cv9 Modern AI-Powered Recruitment Agency.
People Also Ask
What are the top 10 VPNs in the world in 2026?
The top 10 VPNs in 2026 commonly include NordVPN, Surfshark, Proton VPN, ExpressVPN, Private Internet Access, CyberGhost, IPVanish, Mullvad VPN, PureVPN, and Windscribe based on speed, privacy, features, and global reliability.
Which is the best VPN in 2026 for overall performance?
NordVPN is widely regarded as one of the best overall VPNs in 2026 due to its strong speed results, wide server coverage, advanced security tools, and consistent streaming and privacy performance.
Which VPN is fastest in 2026?
IPVanish and NordVPN rank among the fastest VPNs in 2026, with excellent speed retention, low latency, and strong performance for gaming, streaming, and large file downloads.
What is the best VPN for streaming in 2026?
NordVPN, Surfshark, Proton VPN, and PureVPN are among the best VPNs for streaming in 2026 because they show strong success rates for unblocking major streaming platforms across multiple regions.
Which VPN is best for privacy in 2026?
Proton VPN and Mullvad VPN are top choices for privacy in 2026 because of their transparency, no-logs policies, privacy-focused jurisdictions, and strong reputations among security-conscious users.
Are VPNs still worth using in 2026?
Yes, VPNs are still worth using in 2026 for privacy, secure browsing, streaming access, safer public Wi-Fi use, and protecting personal data in a more monitored and restricted internet environment.
Which VPN has the best no-logs policy in 2026?
Mullvad VPN, Proton VPN, NordVPN, and Private Internet Access are widely trusted for strong no-logs policies, especially because of independent audits, transparency efforts, or legal proof in court.
What is the best cheap VPN in 2026?
Surfshark and PureVPN are among the best cheap VPNs in 2026 because they offer low introductory prices, strong security features, and good overall performance without high subscription costs.
Which VPN offers unlimited device connections in 2026?
Surfshark, IPVanish, and Windscribe offer unlimited simultaneous connections in 2026, making them excellent choices for families, households, and users with many connected devices.
What is the best VPN for mobile devices in 2026?
NordVPN and Surfshark are leading VPNs for mobile devices in 2026 thanks to highly rated iOS and Android apps, strong mobile security features, and smooth performance on smartphones and tablets.
Which VPN is best for beginners in 2026?
ExpressVPN and CyberGhost are great VPNs for beginners in 2026 because they offer simple apps, easy server selection, and a smooth user experience with minimal setup complexity.
What is the safest VPN to use in 2026?
The safest VPNs in 2026 include NordVPN, Proton VPN, and Mullvad VPN because they combine strong encryption, secure infrastructure, privacy-first design, and independently verified security practices.
Which VPN works best for Netflix in 2026?
NordVPN, Surfshark, Proton VPN, and PureVPN are among the best VPNs for Netflix in 2026 because they perform well for region switching and streaming access across multiple libraries.
Can a VPN improve online privacy in 2026?
A VPN can improve online privacy in 2026 by encrypting internet traffic, hiding your IP address, reducing tracking exposure, and helping protect browsing activity from networks and data collectors.
What is the best VPN for gaming in 2026?
NordVPN, IPVanish, and Proton VPN are strong gaming VPNs in 2026 due to their low ping, fast speeds, and stable connections that help reduce lag and support smoother gameplay.
Which VPN is best for torrenting in 2026?
Proton VPN, NordVPN, and Private Internet Access are among the best VPNs for torrenting in 2026 because they offer strong privacy tools, P2P support, and reliable performance for heavy downloads.
Do VPNs slow down internet speed in 2026?
VPNs can slightly reduce speed, but the best VPNs in 2026 keep the slowdown minimal. Top services often maintain near-native performance, especially on local servers and premium protocols.
What should I look for in the best VPN in 2026?
Look for speed, no-logs policies, independent audits, strong encryption, streaming compatibility, mobile app quality, server coverage, and pricing when choosing the best VPN in 2026.
Which VPN has the most servers in 2026?
Proton VPN and Private Internet Access are often noted for having very large server networks in 2026, giving users better coverage, more location options, and improved traffic distribution.
What is the best VPN for remote work in 2026?
NordVPN, ExpressVPN, and dedicated IP VPN providers are strong choices for remote work in 2026 because they support secure access, stable connections, and better compatibility with business systems.
Which VPN has the best dedicated IP in 2026?
NordVPN, Surfshark, ExpressVPN, and Private Internet Access offer strong dedicated IP options in 2026, helping users with stable access, fewer CAPTCHAs, and reputation-sensitive tasks.
Are free VPNs good enough in 2026?
Some free VPNs are useful, but premium VPNs offer better speed, security, support, and streaming access. Proton VPN and Windscribe are among the better-known options with free plans in 2026.
Which VPN is most transparent in 2026?
Proton VPN and Mullvad VPN are among the most transparent VPNs in 2026 due to open-source apps, clear privacy policies, public audits, and strong reputations for privacy-focused operations.
What is the best VPN for censorship bypass in 2026?
Proton VPN, NordVPN, and Surfshark are strong choices for bypassing censorship in 2026 because they use stealth or obfuscation technologies designed to avoid deep packet inspection.
Which VPN has the best app experience in 2026?
NordVPN, Surfshark, and ExpressVPN stand out for app quality in 2026 thanks to polished interfaces, reliable performance, mobile optimization, and features that are easy to use across devices.
Is a VPN legal to use in 2026?
VPNs are legal in many countries in 2026, but some regions restrict or regulate their use. Users should always check local laws before using a VPN for privacy, work, or streaming.
Which VPN is best for families in 2026?
Surfshark and IPVanish are excellent family VPNs in 2026 because they offer unlimited device connections, easy apps, and enough flexibility to protect multiple devices in one household.
Why do people use VPNs in 2026?
People use VPNs in 2026 for secure browsing, streaming access, safer public Wi-Fi, online privacy, remote work, reduced tracking, and protection from data collection and location-based restrictions.
What is the difference between a shared IP and a dedicated IP VPN?
A shared IP is used by many VPN users, which improves anonymity. A dedicated IP is assigned to one user only, offering more stability, fewer CAPTCHAs, and better compatibility with secure platforms.
Which VPN is best for long-term value in 2026?
Surfshark, NordVPN, and CyberGhost offer strong long-term value in 2026 by combining competitive pricing, solid features, strong security, and reliable performance across everyday use cases.
Sources
Precedence Research
- TheBestVPN
- Thales Group
- Check Point Blog
- SQ Magazine
- Symlex VPN
- Security.org
- PCMag
- Tom’s Guide
- TechRadar
- PCWorld
- International Business Times Australia
- All About Cookies
- Surfshark
- Cybernews
- Top10VPN
- Password Manager
- SoftCircles
- GreyCoder
- USGS Astrogeology
- BestVPN
- Mullvad VPN
- Windscribe

























![Writing A Good CV [6 Tips To Improve Your CV] 6 Tips To Improve Your CV](https://blog.9cv9.com/wp-content/uploads/2020/06/2020-06-02-2-100x70.png)